Connecting securely to remote IoT devices using P2P SSH on a Raspberry Pi is crucial in today's interconnected world. As more devices come online, ensuring data security and privacy has become a top priority for tech enthusiasts and professionals alike. This article will guide you step-by-step through the process of establishing secure connections, downloading necessary software, and optimizing your Raspberry Pi for remote IoT applications.
In an era where IoT (Internet of Things) devices are rapidly expanding, secure connections have never been more important. Whether you're managing smart home systems, industrial automation, or personal projects, understanding how to securely connect remote IoT devices via SSH is essential. This article explores the best practices for achieving this while maintaining robust security protocols.
By the end of this guide, you'll have a comprehensive understanding of how to set up secure P2P SSH connections on your Raspberry Pi, download essential software, and troubleshoot common issues. Let's dive into the world of secure remote IoT connectivity and unlock the full potential of your Raspberry Pi projects.
Read also:Dwayne Johnson Ethnicity Exploring The Roots Of The Rock
Table of Contents
- Introduction to Remote IoT SSH
- Raspberry Pi Setup
- Securing Your IoT Connections
- P2P SSH Connections
- Downloading Necessary Software
- Best Practices for Security
- Troubleshooting Common Issues
- Optimizing Performance
- Real-World Applications
- Conclusion and Next Steps
Introduction to Remote IoT SSH
Remote IoT SSH connections are the backbone of secure device management. Using SSH (Secure Shell) allows you to access and control your IoT devices from anywhere in the world, provided you have an internet connection. This section will introduce you to the basics of SSH and why it's essential for IoT applications.
Why SSH is Crucial:
- SSH provides encrypted communication between devices.
- It ensures data integrity and confidentiality.
- SSH is widely supported across various platforms and devices.
With the increasing number of IoT devices, the importance of secure connections cannot be overstated. By leveraging SSH, you can safeguard your data and maintain control over your devices, even when they are located remotely.
Understanding SSH Basics
SSH is a network protocol that enables secure communication between devices. It uses encryption to protect data during transmission, making it ideal for remote IoT applications. To establish an SSH connection, you need:
- An SSH client (on your local machine).
- An SSH server (on your Raspberry Pi or IoT device).
- A secure network connection.
By following best practices, you can ensure that your SSH connections remain secure and reliable.
Read also:Richard Kiel Net Worth A Comprehensive Exploration Of The Legendary Actors Wealth
Raspberry Pi Setup
Setting up your Raspberry Pi for remote IoT applications involves several key steps. This section will guide you through the process of preparing your Raspberry Pi for secure P2P SSH connections.
Initial Configuration
Before diving into SSH, you need to ensure your Raspberry Pi is properly configured. Here's a checklist to follow:
- Install the latest version of Raspberry Pi OS.
- Update all packages and software.
- Set up a static IP address for your Raspberry Pi.
These steps will lay the foundation for a stable and secure environment.
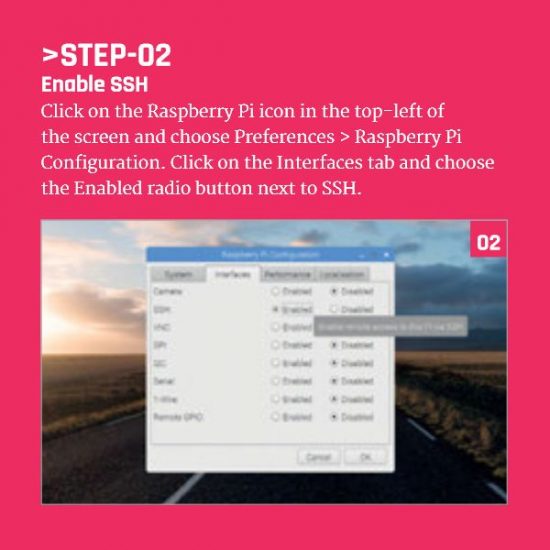
Enabling SSH
To enable SSH on your Raspberry Pi, follow these steps:
- Open the Raspberry Pi Configuration tool.
- Navigate to the "Interfaces" tab.
- Select "Enabled" for SSH.
Once SSH is enabled, you can connect to your Raspberry Pi from any remote location using an SSH client.
Securing Your IoT Connections
Security should always be a top priority when dealing with IoT devices. This section will explore various methods to enhance the security of your remote IoT connections.
Key-Based Authentication
Using key-based authentication instead of passwords adds an extra layer of security to your SSH connections. Here's how you can set it up:
- Generate an SSH key pair on your local machine.
- Copy the public key to your Raspberry Pi.
- Disable password authentication in the SSH configuration file.
This method ensures that only authorized users with the correct private key can access your IoT devices.
Firewall Configuration
Configuring a firewall is another effective way to secure your IoT connections. By restricting access to specific IP addresses or ports, you can minimize the risk of unauthorized access.
P2P SSH Connections
P2P (Peer-to-Peer) SSH connections allow direct communication between devices without relying on a central server. This section will explain how to establish P2P SSH connections for your IoT devices.
Setting Up P2P SSH
To set up P2P SSH connections, you need to:
- Ensure both devices are on the same network.
- Configure SSH to allow connections from specific IP addresses.
- Test the connection to verify it works as expected.
P2P SSH connections are particularly useful for applications where latency and bandwidth are critical factors.
Downloading Necessary Software
Before you can establish secure connections, you need to download and install the necessary software on your Raspberry Pi. This section will guide you through the process.
Popular SSH Clients
There are several SSH clients available, each with its own strengths:
- Putty: A popular choice for Windows users.
- OpenSSH: Pre-installed on most Linux and macOS systems.
- Termius: A cross-platform SSH client for mobile devices.
Choose the client that best suits your needs and install it on your local machine.
Best Practices for Security
Following best practices is essential for maintaining secure IoT connections. This section will outline some key recommendations:
- Regularly update your software and firmware.
- Use strong, unique passwords for all accounts.
- Monitor your devices for suspicious activity.
By adhering to these practices, you can significantly reduce the risk of security breaches.
Troubleshooting Common Issues
Even with careful planning, issues can arise when setting up remote IoT connections. This section will address some common problems and provide solutions:
- Connection Refused: Check your firewall settings and ensure SSH is enabled.
- Authentication Failed: Verify your SSH keys and ensure they match.
- Network Issues: Ensure both devices are connected to the same network.
By troubleshooting these issues, you can quickly resolve problems and maintain secure connections.
Optimizing Performance
Optimizing the performance of your Raspberry Pi is crucial for efficient remote IoT applications. This section will explore ways to enhance its capabilities:
Upgrading Hardware
Consider upgrading your Raspberry Pi's hardware for better performance:
- Add more RAM for improved multitasking.
- Use a faster microSD card for quicker data access.
Tuning SSH Settings
Adjusting SSH settings can also improve performance:
- Disable unused SSH features to reduce overhead.
- Optimize encryption algorithms for faster connections.
These optimizations can lead to more responsive and reliable IoT applications.
Real-World Applications
Secure remote IoT connections have a wide range of applications across various industries. This section will highlight some practical examples:
- Smart Home Systems: Control lighting, temperature, and security systems remotely.
- Industrial Automation: Monitor and manage machinery from a central location.
- Environmental Monitoring: Collect data from sensors deployed in remote locations.
By leveraging secure SSH connections, you can unlock the full potential of IoT technology.
Conclusion and Next Steps
In conclusion, securely connecting remote IoT devices using P2P SSH on a Raspberry Pi is a powerful solution for modern tech enthusiasts. By following the steps outlined in this article, you can ensure that your IoT applications remain secure, reliable, and efficient.
Call to Action:
- Leave a comment below with your thoughts or questions.
- Share this article with others who may find it useful.
- Explore more articles on our site for additional tips and tricks.
Thank you for reading, and happy tinkering!