In today's interconnected world, securely connect remote IoT P2P SSH Windows 10 has become a critical topic for individuals and businesses alike. As more devices are connected to the internet, ensuring secure communication between them is paramount to protect sensitive data and maintain privacy. This guide aims to provide an in-depth understanding of how to establish secure connections using SSH on Windows 10, specifically for remote IoT devices in peer-to-peer (P2P) environments.
With the rise of the Internet of Things (IoT), billions of devices are now capable of communicating with one another. However, this increased connectivity also introduces vulnerabilities that can be exploited by malicious actors. Therefore, implementing robust security measures is essential. In this article, we will explore the best practices for securely connecting remote IoT devices through P2P SSH on Windows 10.
This guide is designed for anyone looking to enhance their knowledge of IoT security and learn how to set up secure connections using SSH. Whether you're a developer, system administrator, or simply someone interested in cybersecurity, this article will provide valuable insights and actionable steps to safeguard your IoT infrastructure.
Read also:Amariah Morales The Rising Star In The Spotlight
Table of Contents
- Introduction to Secure IoT Connections
- What is SSH and Why Use It for IoT?
- Understanding Remote IoT Connections
- Peer-to-Peer (P2P) Connections in IoT
- Setting Up SSH on Windows 10
- Best Practices for Secure Connections
- Configuring Firewalls for Enhanced Security
- Encryption Methods for Data Protection
- Troubleshooting Common Issues
- Conclusion and Next Steps
Introduction to Secure IoT Connections
The foundation of any secure IoT setup lies in establishing reliable and encrypted connections. Securely connect remote IoT P2P SSH Windows 10 ensures that data transmitted between devices remains private and tamper-proof. In this section, we'll explore the importance of secure connections in IoT environments and why SSH is a preferred protocol for this purpose.
Why Security Matters in IoT
IoT devices collect and transmit vast amounts of data, much of which can be sensitive or personally identifiable. A lack of proper security measures can lead to data breaches, unauthorized access, and even physical harm in some cases. By securely connecting remote IoT devices, you can mitigate these risks and ensure the integrity of your network.
Key Benefits of Secure Connections
- Protection against cyberattacks
- Preservation of data privacy
- Enhanced reliability and performance
- Compliance with industry regulations
What is SSH and Why Use It for IoT?
SSH, or Secure Shell, is a cryptographic network protocol used to securely connect to remote devices over an unsecured network. It provides a secure channel for data transmission, making it ideal for IoT applications where sensitive information is involved. In this section, we'll delve into the workings of SSH and its advantages for IoT devices.
How SSH Works
SSH uses encryption algorithms to secure data during transmission. It establishes a secure connection through authentication methods such as passwords or public key cryptography. This ensures that only authorized users can access the devices, reducing the risk of unauthorized access.
Advantages of SSH for IoT
- Strong encryption for data protection
- Reliable authentication mechanisms
- Compatibility with various operating systems
- Wide range of supported commands and protocols
Understanding Remote IoT Connections
Remote IoT connections enable devices to communicate with each other even when they are physically distant. Securely connect remote IoT P2P SSH Windows 10 allows for seamless interaction between devices without compromising security. In this section, we'll discuss the challenges and solutions associated with remote IoT connections.
Challenges of Remote IoT Connections
Some common challenges include network latency, bandwidth limitations, and potential security vulnerabilities. To address these issues, it's crucial to implement robust security protocols and optimize network configurations.
Read also:Alana Cho A Rising Star In The Entertainment Industry
Solutions for Secure Remote Connections
- Use of SSH for encrypted communication
- Implementation of firewalls and intrusion detection systems
- Regular updates and patches for devices and software
Peer-to-Peer (P2P) Connections in IoT
Peer-to-peer (P2P) connections allow IoT devices to communicate directly with one another without relying on a central server. This architecture offers several advantages, including reduced latency and improved scalability. In this section, we'll explore how P2P connections can enhance IoT networks when combined with SSH.
Advantages of P2P Connections
- Reduced reliance on centralized infrastructure
- Improved efficiency and performance
- Enhanced resilience against network failures
Securing P2P Connections with SSH
By integrating SSH into P2P connections, you can ensure that data exchanged between devices remains secure and private. This combination provides a robust framework for secure communication in IoT environments.
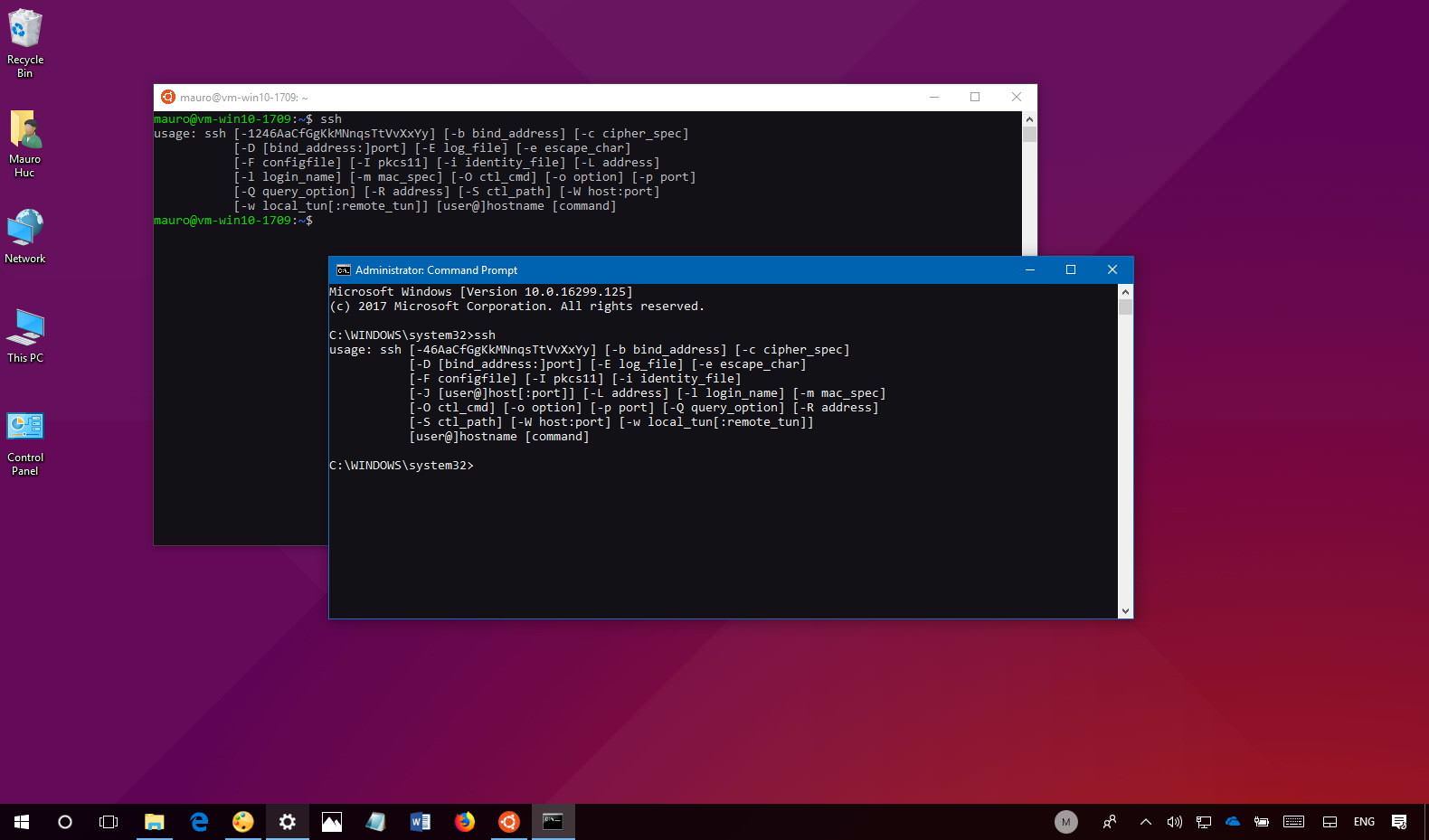
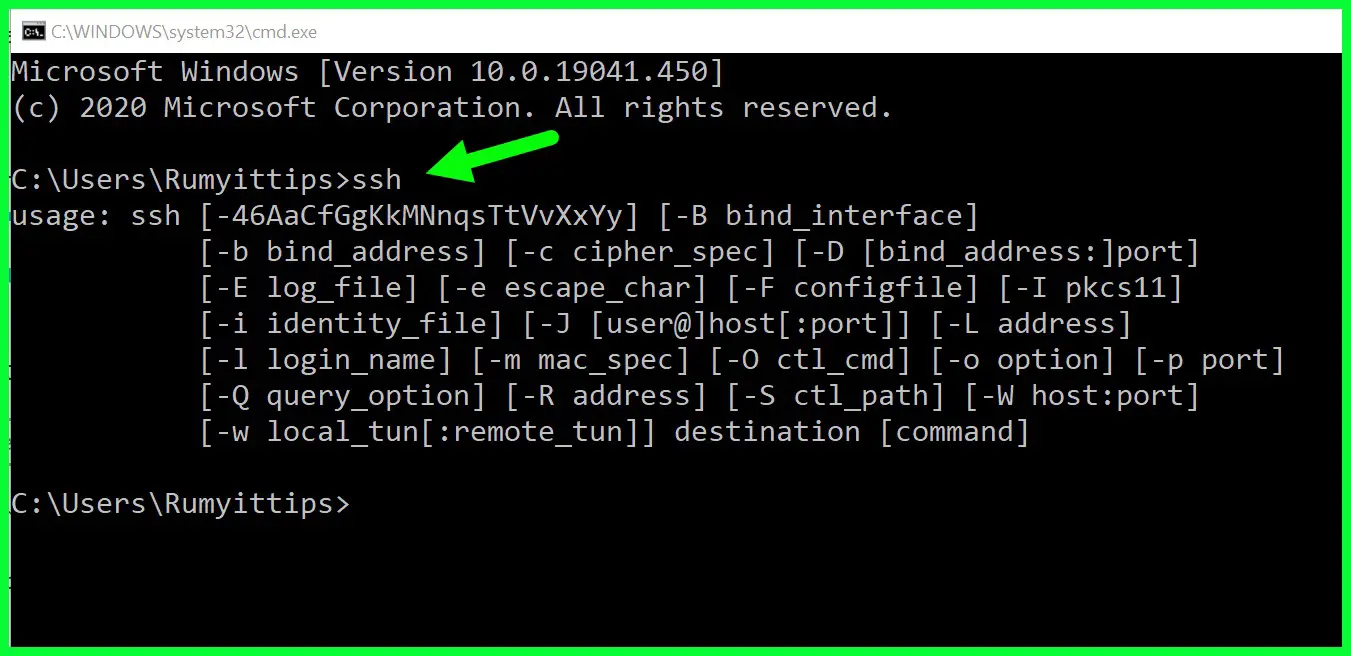
Setting Up SSH on Windows 10
Windows 10 includes built-in support for SSH, making it easier than ever to securely connect remote IoT devices. In this section, we'll walk you through the process of enabling and configuring SSH on Windows 10.
Enabling SSH on Windows 10
To enable SSH on Windows 10, follow these steps:
- Open the "Settings" app
- Navigate to "Apps"> "Optional features"
- Click on "Add a feature" and search for "OpenSSH Client"
- Select "OpenSSH Client" and click "Install"
Configuring SSH Settings
Once SSH is enabled, you can configure its settings to suit your needs. This includes setting up authentication methods, defining access permissions, and configuring encryption protocols.
Best Practices for Secure Connections
Implementing best practices for secure connections is essential to protect your IoT devices and network. In this section, we'll outline key strategies for enhancing security when securely connect remote IoT P2P SSH Windows 10.
Use Strong Authentication Methods
Instead of relying solely on passwords, consider using public key authentication for SSH. This method provides stronger security and reduces the risk of brute-force attacks.
Regularly Update Devices and Software
Keeping your devices and software up to date is crucial for addressing security vulnerabilities. Regular updates ensure that your system is protected against the latest threats.
Configuring Firewalls for Enhanced Security
Firewalls play a critical role in securing IoT networks by controlling incoming and outgoing traffic. In this section, we'll discuss how to configure firewalls to enhance the security of your SSH connections.
Firewall Rules for SSH
Set up specific firewall rules to allow SSH traffic while blocking unauthorized access. This includes defining port numbers, IP addresses, and access permissions.
Monitoring Firewall Logs
Regularly monitor firewall logs to detect and respond to suspicious activity. This proactive approach helps identify potential security threats before they can cause harm.
Encryption Methods for Data Protection
Encryption is a fundamental aspect of securing IoT connections. In this section, we'll explore different encryption methods and their applications in IoT environments.
Common Encryption Protocols
- AES (Advanced Encryption Standard)
- RSA (Rivest-Shamir-Adleman)
- Elliptic Curve Cryptography (ECC)
Choosing the Right Encryption Method
Selecting the appropriate encryption method depends on factors such as performance requirements, resource constraints, and security needs. Evaluate these factors to determine the best encryption solution for your IoT setup.
Troubleshooting Common Issues
Even with the best security measures in place, issues can arise. In this section, we'll provide tips for troubleshooting common problems related to securely connect remote IoT P2P SSH Windows 10.
Connection Issues
If you encounter connection problems, check the following:
- Ensure SSH is enabled and properly configured
- Verify firewall settings and port availability
- Test network connectivity and latency
Authentication Failures
Authentication issues can often be resolved by:
- Verifying username and password credentials
- Checking public key configurations
- Reviewing access permissions and user roles
Conclusion and Next Steps
In conclusion, securely connect remote IoT P2P SSH Windows 10 is a vital aspect of modern IoT infrastructure. By following the guidelines and best practices outlined in this article, you can ensure the security and reliability of your IoT network. Remember to regularly update your devices, monitor network activity, and implement robust encryption methods to protect against potential threats.
We encourage you to take action by implementing the strategies discussed in this guide. Share your thoughts and experiences in the comments section below, and feel free to explore other articles on our site for more insights into IoT security and related topics. Together, we can build a safer and more connected world.