In the era of interconnected devices, the ability to securely connect remote IoT devices using peer-to-peer (P2P) SSH on a Raspberry Pi has become a necessity. Whether you're a tech enthusiast or a professional developer, this guide will provide you with comprehensive insights into achieving secure connections without breaking the bank. This article is designed to ensure you have the most reliable methods to protect your IoT infrastructure while keeping costs low.
As technology continues to evolve, more devices are being connected to the internet, creating a vast network of IoT devices. However, with this connectivity comes the challenge of ensuring security. Protecting your data and devices from unauthorized access is critical, and using SSH on Raspberry Pi can help you achieve that.
This guide will explore the best ways to set up secure remote IoT connections using P2P SSH on Raspberry Pi, ensuring your network remains safe and efficient. Let's dive in and discover how you can achieve this without spending a dime.
Read also:Anna Faris The Journey Of A Multitalented Star
Table of Contents
- Introduction
- Understanding SSH
- Raspberry Pi Overview
- Why Secure Remote IoT Connections Matter
- Step-by-Step Guide to Setting Up P2P SSH
- Best Practices for Securing SSH
- Common Mistakes to Avoid
- Tools and Software for Free SSH
- Cost-Effective Solutions for IoT Security
- Conclusion
Introduction
In today's digital age, the demand for secure remote access to IoT devices has skyrocketed. With the increasing number of connected devices, ensuring the safety and integrity of your data is paramount. The Raspberry Pi, a versatile and affordable single-board computer, offers an excellent platform for setting up secure remote connections using SSH.
SSH (Secure Shell) is a cryptographic network protocol that provides secure communication over an unsecured network. It is widely used for remote command-line login and other secure network services. By leveraging SSH on Raspberry Pi, you can establish a secure connection to your IoT devices, ensuring your data remains protected.
This article will guide you through the process of setting up a secure remote IoT P2P SSH connection on Raspberry Pi for free, helping you safeguard your network without incurring additional costs.
Understanding SSH
What is SSH?
SSH, or Secure Shell, is a protocol that encrypts data transmitted between two devices, ensuring secure communication. It is primarily used for remote access to servers and devices, allowing users to execute commands and transfer files securely.
Key features of SSH include:
- Encryption of data during transmission
- Authentication mechanisms to verify user identity
- Support for secure file transfers
Why Use SSH for IoT Devices?
IoT devices are often deployed in remote locations, making secure remote access essential. SSH provides a robust solution for managing these devices, ensuring that data transmitted between the device and the user remains confidential and tamper-proof.
Read also:Marie Temara The Rising Star In The World Of Beauty And Content Creation
By using SSH, you can:
- Remotely manage and configure IoT devices
- Securely transfer files to and from the device
- Protect sensitive data from unauthorized access
Raspberry Pi Overview
The Raspberry Pi is a compact and affordable single-board computer that has gained immense popularity among developers and hobbyists. It is a versatile platform that can be used for a wide range of applications, from home automation to industrial IoT solutions.
Key features of the Raspberry Pi include:
- Low cost and energy-efficient
- Support for multiple operating systems
- Extensive community support and resources
Why Secure Remote IoT Connections Matter
As the number of IoT devices continues to grow, so does the risk of cyberattacks. Secure remote connections are essential to protect your devices and data from unauthorized access. By implementing SSH on Raspberry Pi, you can ensure that your IoT network remains safe and secure.
Benefits of secure remote IoT connections include:
- Protection against cyber threats
- Improved data privacy and integrity
- Enhanced network reliability
Step-by-Step Guide to Setting Up P2P SSH
Step 1: Install SSH on Raspberry Pi
The first step in setting up P2P SSH is to install the SSH server on your Raspberry Pi. This can be done by running the following command in the terminal:
sudo apt-get install openssh-server
Step 2: Configure SSH Settings
Once SSH is installed, you can configure its settings by editing the SSH configuration file. Use the following command to open the file:
sudo nano /etc/ssh/sshd_config
Make the necessary changes to enhance security, such as disabling root login and changing the default port.
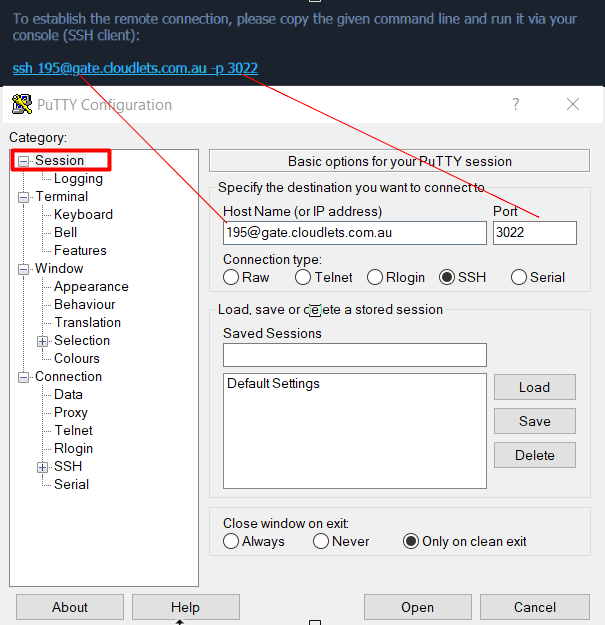
Step 3: Connect to Your Raspberry Pi
To connect to your Raspberry Pi remotely, you will need an SSH client. Popular options include PuTTY for Windows and the built-in terminal on macOS and Linux. Use the following command to connect:
ssh username@raspberrypi.local
Best Practices for Securing SSH
While SSH provides a secure method for remote access, there are additional steps you can take to enhance its security:
- Use strong passwords or SSH keys for authentication
- Disable password authentication and use SSH keys exclusively
- Limit access to specific IP addresses
- Regularly update your Raspberry Pi's operating system and software
Common Mistakes to Avoid
When setting up SSH on Raspberry Pi, it's essential to avoid common mistakes that could compromise your security:
- Using weak passwords or default credentials
- Failing to update software and firmware regularly
- Not securing your network with a firewall
Tools and Software for Free SSH
Several tools and software are available for setting up SSH on Raspberry Pi without incurring additional costs:
- OpenSSH: A widely used and free SSH server and client
- SSHFS: A file system client that allows you to mount remote directories over SSH
- TunnelBear: A free SSH tunneling service for secure connections
Cost-Effective Solutions for IoT Security
Implementing secure remote IoT connections doesn't have to be expensive. By leveraging free tools and software, you can achieve robust security without breaking the bank. Some cost-effective solutions include:
- Using open-source software for SSH and network management
- Implementing basic security measures such as firewalls and encryption
- Regularly monitoring your network for potential threats
Conclusion
In conclusion, setting up a secure remote IoT P2P SSH connection on Raspberry Pi is a cost-effective way to protect your devices and data. By following the steps outlined in this guide and adhering to best practices, you can ensure that your IoT network remains safe and reliable.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more tips and tricks on IoT security and Raspberry Pi projects.