In today's digital age, securely connect remote IoT P2P free Raspberry Pi download has become an essential topic for tech enthusiasts and professionals alike. The rise of Internet of Things (IoT) devices has transformed the way we interact with technology, making it crucial to understand how to establish secure connections between devices. Whether you're a hobbyist or a seasoned developer, learning how to create a peer-to-peer (P2P) network for remote IoT devices using a Raspberry Pi can open doors to countless possibilities.
As more devices become interconnected, the need for secure communication channels becomes paramount. This guide will delve into the intricacies of setting up a secure remote IoT P2P connection using a Raspberry Pi. We'll explore the tools, software, and best practices necessary to ensure your IoT devices are protected from potential threats while maintaining seamless connectivity.
By the end of this article, you'll have a comprehensive understanding of how to download and configure the necessary software to create a secure P2P connection for your IoT devices. Whether you're looking to enhance your home automation system or build a professional-grade IoT network, this guide will provide you with the knowledge and resources you need to succeed.
Read also:Judy Garland Height A Comprehensive Look At The Iconic Star
Table of Contents
- Introduction to Remote IoT P2P Connections
- Raspberry Pi Overview
- Why Secure Connections Matter
- Tools and Software for Secure Connections
- Step-by-Step Guide to Setting Up P2P
- Best Practices for IoT Security
- Troubleshooting Common Issues
- Future Trends in IoT Security
- Real-World Applications of IoT P2P
- Conclusion
Introduction to Remote IoT P2P Connections
The concept of remote IoT P2P connections revolves around enabling devices to communicate directly with one another without relying on centralized servers. This approach offers numerous advantages, including reduced latency, enhanced privacy, and improved efficiency. By leveraging a Raspberry Pi as the central hub for your IoT network, you can create a secure and reliable P2P connection that ensures your devices remain connected and protected.
What is IoT?
IoT refers to the network of physical objects embedded with sensors, software, and connectivity capabilities, allowing them to exchange data with other devices and systems over the internet. From smart home appliances to industrial machinery, IoT devices are transforming various industries by providing real-time insights and automation capabilities.
Why Choose Raspberry Pi?
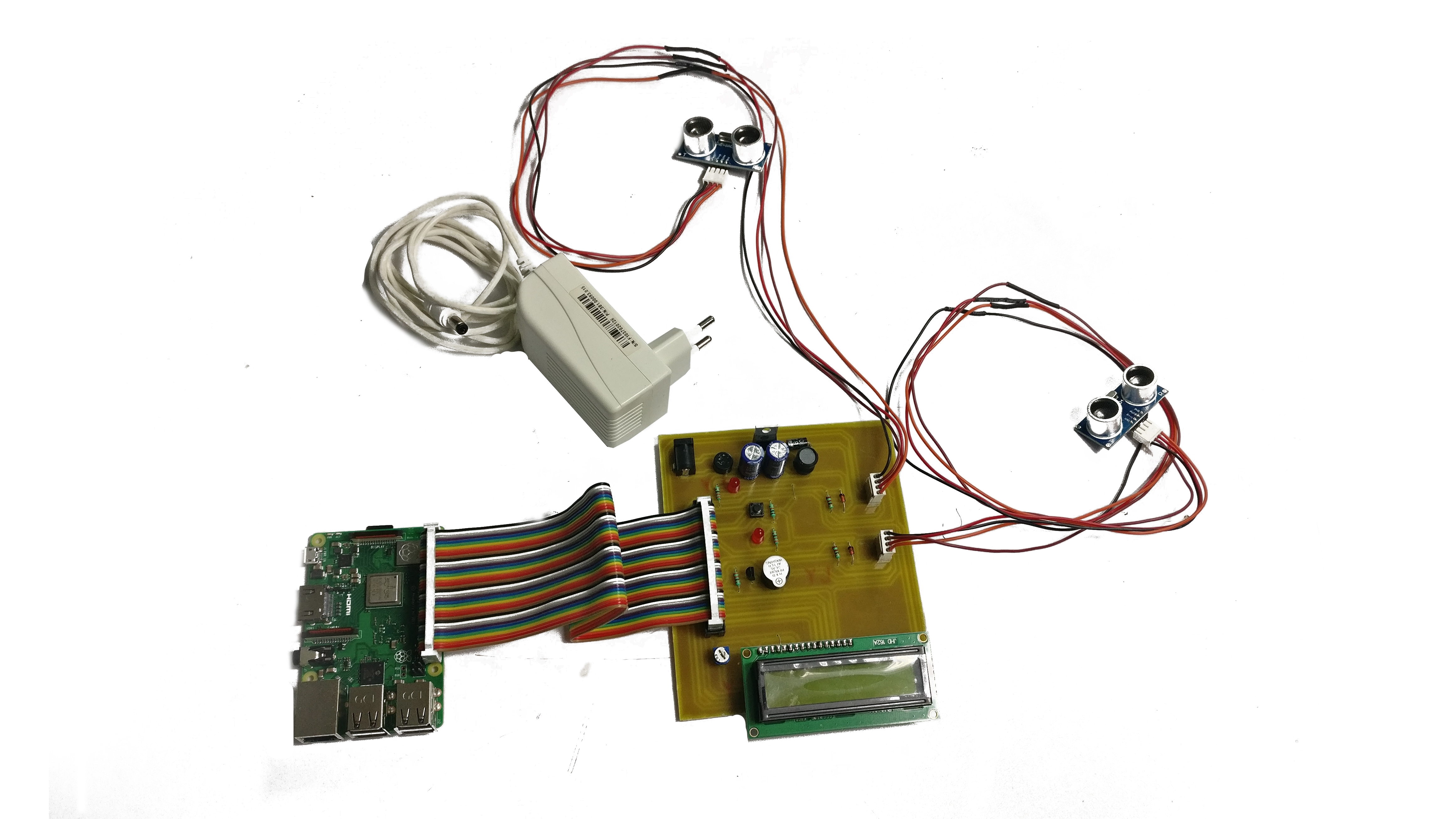
Raspberry Pi is a versatile and cost-effective single-board computer that has gained immense popularity among developers and hobbyists. Its small form factor, low power consumption, and compatibility with a wide range of software make it an ideal choice for building IoT networks. Additionally, its open-source nature allows for extensive customization and integration with third-party tools.
Raspberry Pi Overview
Raspberry Pi is a series of small single-board computers developed by the Raspberry Pi Foundation. Initially designed to promote computer science education, it has since evolved into a powerful tool for various applications, including IoT development. The latest models, such as the Raspberry Pi 4, offer impressive performance and connectivity options, making them suitable for demanding tasks like creating secure P2P networks.
Key Features of Raspberry Pi
- Compact size and low power consumption
- Support for multiple operating systems, including Raspbian and Ubuntu
- Built-in Wi-Fi and Bluetooth for wireless connectivity
- GPIO pins for interfacing with external devices
- Compatibility with a wide range of accessories and expansion boards
Why Secure Connections Matter
In the realm of IoT, security should always be a top priority. As more devices become connected, the risk of cyberattacks and data breaches increases exponentially. Establishing secure connections between IoT devices is essential to protect sensitive information and prevent unauthorized access. By implementing robust security measures, you can ensure the integrity and confidentiality of your IoT network.
Common IoT Security Threats
- Data interception and eavesdropping
- Denial-of-service (DoS) attacks
- Firmware vulnerabilities
- Malware and ransomware infections
Tools and Software for Secure Connections
Creating a secure remote IoT P2P connection requires the right tools and software. Below are some essential components you'll need to get started:
Read also:George Conway Iv A Comprehensive Look At His Life Career And Achievements
Operating Systems
For Raspberry Pi, Raspbian is the recommended operating system due to its optimized performance and extensive support. However, other options like Ubuntu and Arch Linux are also viable depending on your specific requirements.
Encryption Protocols
Implementing strong encryption protocols is crucial for securing your IoT network. Popular choices include:
- SSL/TLS for securing data in transit
- SSH for secure remote access
- IPsec for securing IP communications
Step-by-Step Guide to Setting Up P2P
Now that you have a basic understanding of the tools and software required, let's walk through the process of setting up a secure remote IoT P2P connection using a Raspberry Pi:
Step 1: Prepare Your Raspberry Pi
Begin by installing the desired operating system on your Raspberry Pi. Ensure that all necessary drivers and firmware are up to date to avoid compatibility issues.
Step 2: Configure Network Settings
Set up your Raspberry Pi to connect to your local network. This may involve configuring Wi-Fi or Ethernet settings depending on your setup.
Step 3: Install Required Software
Download and install the necessary software for establishing a secure P2P connection. This may include encryption tools, communication libraries, and any additional packages required for your specific use case.
Step 4: Establish the P2P Connection
Using the installed software, configure your IoT devices to communicate directly with one another via the Raspberry Pi. Ensure that all security settings are properly configured to protect your network.
Best Practices for IoT Security
Adhering to best practices is essential for maintaining a secure IoT network. Below are some key recommendations:
- Regularly update firmware and software to patch vulnerabilities
- Use strong, unique passwords for all devices and accounts
- Enable two-factor authentication whenever possible
- Monitor network activity for signs of suspicious behavior
Troubleshooting Common Issues
Even with careful planning, issues may arise when setting up a secure remote IoT P2P connection. Below are some common problems and their solutions:
Issue: Unable to Connect Devices
Solution: Verify that all devices are properly configured and connected to the same network. Check for any firewall or security settings that may be blocking communication.
Issue: Slow Data Transfer
Solution: Optimize your network settings to improve performance. Consider upgrading your hardware if necessary to handle increased data loads.
Future Trends in IoT Security
As technology continues to evolve, so too will the methods used to secure IoT networks. Emerging trends such as blockchain-based security, quantum cryptography, and artificial intelligence-driven threat detection promise to enhance the safety and reliability of IoT devices. Staying informed about these advancements will help you stay ahead of potential threats and ensure your network remains protected.
Real-World Applications of IoT P2P
IoT P2P connections have numerous practical applications across various industries. Some examples include:
- Smart home automation systems
- Industrial machine monitoring and control
- Agricultural sensor networks for crop management
- Healthcare devices for remote patient monitoring
Conclusion
Securing remote IoT P2P connections using a Raspberry Pi is a powerful way to enhance the functionality and safety of your IoT network. By following the steps outlined in this guide and adhering to best practices, you can create a robust and reliable system that meets your specific needs. Remember to stay vigilant and keep up with the latest developments in IoT security to ensure your network remains protected against emerging threats.
We encourage you to share your thoughts and experiences in the comments below. Have you successfully implemented a secure IoT P2P connection using a Raspberry Pi? What challenges did you face, and how did you overcome them? Your input can help others in the community learn and grow. Don't forget to explore our other articles for more insights into the world of IoT and technology.