In the era of interconnected devices, securely connecting a remote IoT using peer-to-peer (P2P) SSH on a Raspberry Pi has become a crucial skill for tech enthusiasts and professionals alike. With the increasing demand for remote access solutions, ensuring security without breaking the bank is more important than ever. This guide will walk you through the best methods to achieve secure connectivity while keeping costs at zero.
As more businesses and individuals adopt IoT devices, the need for secure communication between these devices becomes paramount. One of the most reliable ways to do this is by leveraging SSH (Secure Shell) on a Raspberry Pi. SSH ensures encrypted communication, which is essential for protecting sensitive data.
This article is designed to provide you with a comprehensive understanding of how to set up a secure remote IoT connection using P2P SSH on a Raspberry Pi. Whether you're a beginner or an advanced user, this guide will cater to your needs by offering step-by-step instructions, expert tips, and reliable references.
Read also:Dwayne Johnson Ethnicity Exploring The Roots Of The Rock
Table of Contents
- Introduction to SSH and Its Importance
- Overview of Raspberry Pi for IoT
- Setting Up SSH on Raspberry Pi
- Securing Your SSH Connection
- Establishing a P2P SSH Connection
- Enabling Remote Access for IoT Devices
- Free Tools to Enhance Security
- Common Issues and Solutions
- Best Practices for Secure IoT Connections
- Conclusion
Introduction to SSH and Its Importance
SSH, or Secure Shell, is a cryptographic network protocol used for secure communication between devices over an unsecured network. It provides a robust layer of encryption, ensuring that data transmitted between devices remains private and tamper-proof.
Why SSH is Essential for IoT
IoT devices are often deployed in environments where they need to communicate with remote servers or other devices. Without proper security measures, these devices can become vulnerable to cyberattacks. SSH offers a secure channel for data exchange, making it indispensable for IoT applications.
Overview of Raspberry Pi for IoT
The Raspberry Pi is a versatile, low-cost, single-board computer that has become a favorite among hobbyists and professionals for IoT projects. Its compact size, affordability, and compatibility with various software make it ideal for setting up secure remote connections.
Key Features of Raspberry Pi
- Compact and lightweight design
- Supports multiple operating systems
- Rich community support for troubleshooting and development
- Capable of running SSH servers for secure connections
Setting Up SSH on Raspberry Pi
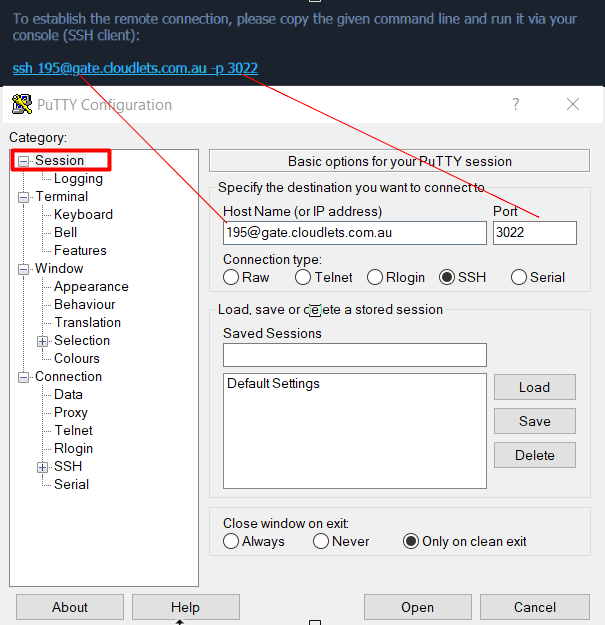
Configuring SSH on a Raspberry Pi is a straightforward process. By following these steps, you can enable SSH and prepare your device for secure remote access.
Step-by-Step Guide
- Install the latest version of Raspberry Pi OS on your device.
- Access the terminal and enter the command
sudo raspi-config. - Navigate to the "Interfacing Options" menu and enable SSH.
- Reboot your Raspberry Pi to apply the changes.
Securing Your SSH Connection
Once SSH is enabled, it's crucial to implement security measures to protect your connection from unauthorized access. Here are some effective strategies:
Best Security Practices
- Change the default SSH port to a non-standard number.
- Use strong, unique passwords or public key authentication.
- Disable root login to prevent brute-force attacks.
- Install a firewall to restrict access to specific IP addresses.
Establishing a P2P SSH Connection
A peer-to-peer (P2P) SSH connection allows direct communication between two devices without the need for a central server. This setup is particularly useful for IoT applications where devices need to communicate securely and efficiently.
Read also:Edgar Buchanan Net Worth Exploring The Wealth And Legacy Of A Hollywood Legend
How P2P SSH Works
P2P SSH leverages tunneling techniques to create a direct link between devices. By bypassing intermediaries, this method reduces latency and enhances security. To establish a P2P SSH connection:
- Configure both devices to use the same SSH keys.
- Set up port forwarding on your router for direct access.
- Test the connection using the
sshcommand with the appropriate IP address.
Enabling Remote Access for IoT Devices
Remote access is a critical feature for managing IoT devices from anywhere in the world. By combining SSH with other tools, you can create a secure and reliable remote access solution.
Tools for Remote Access
- ngrok: A free tool that provides secure tunnels to localhost.
- Tailscale: A peer-to-peer mesh network that simplifies remote access.
- WireGuard: A modern VPN solution that integrates well with SSH.
Free Tools to Enhance Security
Several free tools are available to enhance the security of your SSH connections. These tools complement the built-in features of SSH and provide additional layers of protection.
Top Free Tools
- Fail2Ban: Prevents brute-force attacks by blocking malicious IP addresses.
- UFW (Uncomplicated Firewall): Simplifies firewall configuration for SSH.
- OpenSSH: The standard SSH server software that comes pre-installed on most Linux distributions.
Common Issues and Solutions
While setting up SSH on a Raspberry Pi, you may encounter various challenges. Here are some common issues and their solutions:
Troubleshooting Tips
- Connection Refused: Ensure SSH is enabled and the correct port is being used.
- Authentication Failed: Double-check your SSH keys and password.
- Network Issues: Verify your router settings and IP configuration.
Best Practices for Secure IoT Connections
To ensure the highest level of security for your IoT devices, follow these best practices:
Key Recommendations
- Regularly update your Raspberry Pi OS and SSH software.
- Monitor logs for suspicious activity and take immediate action if necessary.
- Limit access to trusted devices and users only.
Conclusion
Securing remote IoT connections using P2P SSH on a Raspberry Pi is an essential skill in today's interconnected world. By following the steps outlined in this guide, you can achieve secure connectivity without incurring any costs. Remember to implement best practices and use reliable tools to enhance your security posture.
We encourage you to share your experiences and insights in the comments section below. Additionally, feel free to explore other articles on our site for more tips and tricks related to IoT and cybersecurity.
Data Sources: