Connecting your IoT devices securely has never been more important as the world becomes increasingly interconnected. With the rise of remote work, smart homes, and industrial automation, ensuring a secure connection between devices is critical. One of the most popular ways to achieve this is by leveraging Raspberry Pi for creating peer-to-peer (P2P) connections. In this article, we will explore how you can securely connect remote IoT devices using P2P technology with Raspberry Pi, offering free downloads and step-by-step instructions.
In today's fast-paced digital era, the Internet of Things (IoT) has revolutionized the way we interact with technology. From wearable devices to smart appliances, IoT devices are everywhere. However, the challenge lies in ensuring that these devices are connected securely without compromising performance or privacy. This is where Raspberry Pi comes into play, offering an affordable and flexible solution for secure remote IoT P2P connections.
Whether you're a hobbyist, a developer, or a business owner, understanding how to securely connect IoT devices using Raspberry Pi can significantly enhance your projects. This article will guide you through the process, providing valuable insights, tips, and resources to help you achieve seamless and secure connectivity.
Read also:Mika Lafuente X Unveiling The Rising Star In The Digital Era
Table of Contents
- Introduction to Secure IoT Connections
- Benefits of Using Raspberry Pi for IoT
- Understanding P2P Technology for IoT
- Steps to Securely Connect IoT Devices
- Free Downloads and Resources
- Setting Up Remote Access
- Best Practices for Secure Connections
- Common Issues and Troubleshooting
- Real-World Case Studies
- Conclusion and Call to Action
Introduction to Secure IoT Connections
IoT devices have transformed the way we live and work, but with this transformation comes the need for robust security measures. Securely connecting remote IoT devices is essential to protect sensitive data and prevent unauthorized access. In this section, we'll explore why security is crucial and how Raspberry Pi can help.
The primary goal of secure IoT connections is to ensure that data transmitted between devices remains private and tamper-proof. This involves implementing encryption protocols, secure authentication methods, and regular updates to address vulnerabilities. Raspberry Pi, with its open-source nature and flexibility, offers an excellent platform for achieving these objectives.
Why Choose Raspberry Pi for IoT?
- Affordable hardware
- Extensive community support
- Compatibility with various operating systems
- Customizable configurations
Benefits of Using Raspberry Pi for IoT
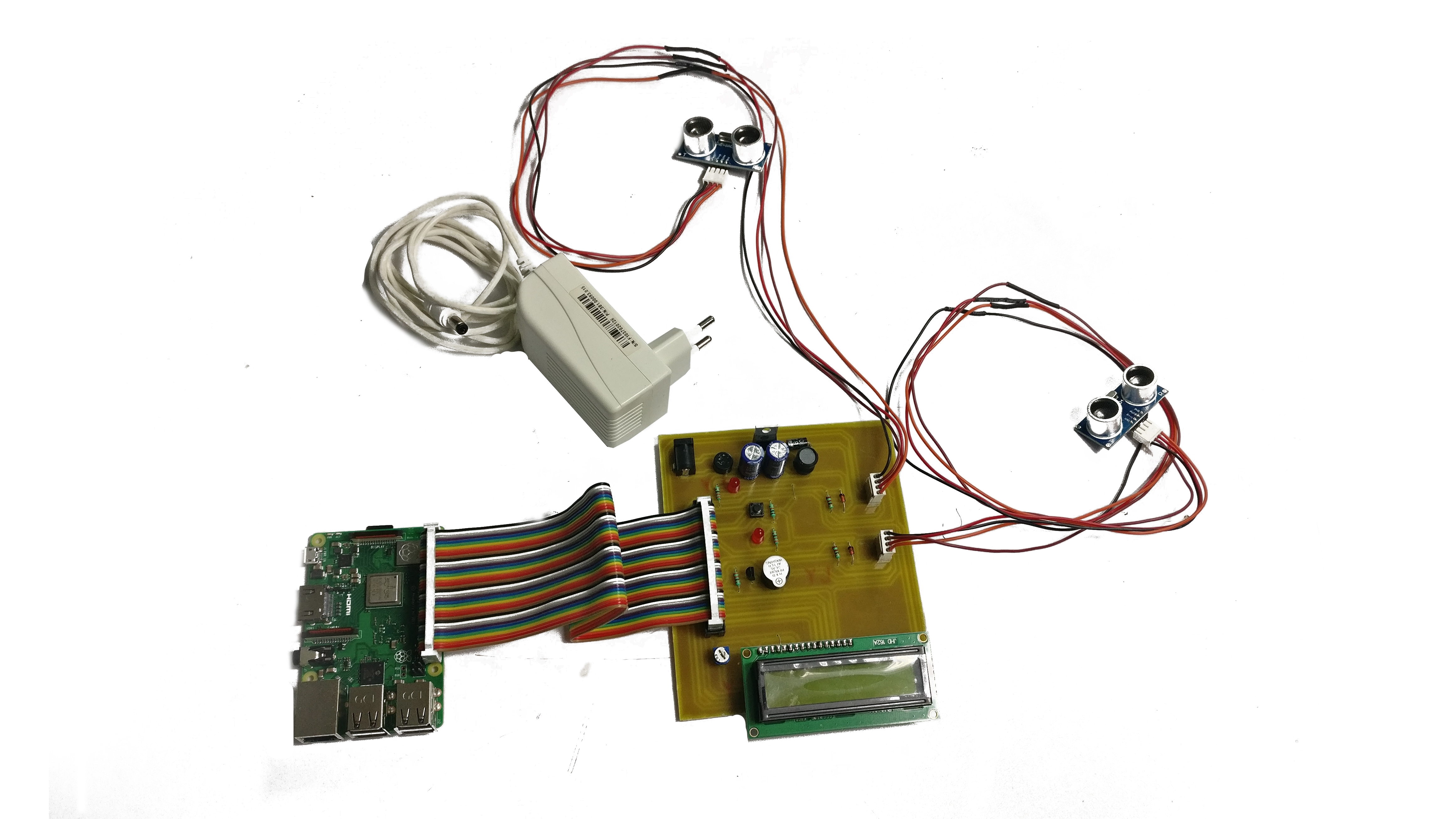
Raspberry Pi is a versatile single-board computer that has gained immense popularity among developers and hobbyists alike. Its affordability, ease of use, and powerful capabilities make it an ideal choice for IoT projects. Let's delve into the benefits of using Raspberry Pi for secure IoT connections.
Raspberry Pi offers a range of features that enhance its suitability for IoT applications. From its ability to run lightweight operating systems to its compatibility with a wide array of sensors and peripherals, Raspberry Pi provides a robust foundation for building secure IoT systems.
Key Features of Raspberry Pi
- Powerful processing capabilities
- Low power consumption
- Wide range of GPIO pins for interfacing
- Support for multiple programming languages
Understanding P2P Technology for IoT
Peer-to-peer (P2P) technology eliminates the need for centralized servers, allowing devices to communicate directly with each other. This decentralized approach enhances security and reduces latency, making it ideal for IoT applications. In this section, we'll discuss the fundamentals of P2P technology and its applications in IoT.
P2P networks are particularly beneficial for IoT devices as they reduce reliance on cloud infrastructure, which can be vulnerable to attacks. By establishing direct connections between devices, P2P technology ensures faster and more secure communication.
Read also:Alana Cho A Rising Star In The Entertainment Industry
Advantages of P2P in IoT
- Enhanced security through direct connections
- Reduced latency for real-time applications
- Lower costs due to reduced server requirements
Steps to Securely Connect IoT Devices
Securing IoT devices involves multiple steps, from configuring encryption protocols to implementing strong authentication mechanisms. In this section, we'll outline the key steps required to securely connect IoT devices using Raspberry Pi.
Step 1: Install a Secure Operating System
Begin by installing a secure operating system on your Raspberry Pi. Popular choices include Raspbian and Ubuntu Server, both of which offer robust security features.
Step 2: Configure Encryption Protocols
Enable encryption protocols such as TLS or SSH to secure data transmission between devices. This ensures that sensitive information remains protected during transit.
Step 3: Implement Authentication Mechanisms
Set up strong authentication mechanisms, such as username/password combinations or multi-factor authentication, to prevent unauthorized access to your IoT devices.
Free Downloads and Resources
Accessing free resources and downloads can significantly enhance your IoT projects. In this section, we'll provide links to valuable resources and tools that can help you securely connect IoT devices using Raspberry Pi.
Some of the recommended resources include:
Setting Up Remote Access
Remote access to IoT devices is crucial for monitoring and managing them effectively. In this section, we'll explore how to set up remote access using Raspberry Pi, ensuring that it remains secure and reliable.
One of the most popular methods for remote access is using SSH (Secure Shell), which provides encrypted communication between devices. By configuring SSH on your Raspberry Pi, you can securely access your IoT devices from anywhere in the world.
Configuring SSH on Raspberry Pi
To enable SSH on your Raspberry Pi, follow these steps:
- Open the terminal on your Raspberry Pi.
- Run the command
sudo raspi-config. - Navigate to "Interfacing Options" and enable SSH.
- Reboot your Raspberry Pi to apply the changes.
Best Practices for Secure Connections
Adhering to best practices is essential for maintaining secure IoT connections. In this section, we'll discuss some of the best practices for securing your IoT devices when using Raspberry Pi.
Regular Software Updates
Keep your Raspberry Pi and connected devices up to date with the latest software updates. This ensures that any vulnerabilities are promptly addressed, reducing the risk of attacks.
Strong Password Policies
Implement strong password policies, using complex passwords and changing them regularly. Avoid using default passwords and consider using a password manager for added security.
Common Issues and Troubleshooting
Despite taking all necessary precautions, issues may arise when setting up secure IoT connections. In this section, we'll address some common problems and provide troubleshooting tips.
Some of the most common issues include:
- Connection failures due to incorrect configurations
- Authentication errors caused by weak passwords
- Network instability affecting device communication
Real-World Case Studies
Examining real-world case studies can provide valuable insights into the practical applications of secure IoT connections using Raspberry Pi. In this section, we'll explore some successful implementations of this technology.
Case studies highlight the effectiveness of using Raspberry Pi for IoT projects, showcasing its versatility and reliability in various industries, including healthcare, agriculture, and smart cities.
Conclusion and Call to Action
In conclusion, securely connecting remote IoT devices using P2P technology with Raspberry Pi offers numerous benefits, including enhanced security, reduced latency, and cost-effectiveness. By following the steps outlined in this article, you can create a robust and secure IoT system tailored to your needs.
We encourage you to take action by experimenting with the resources and tools provided. Share your experiences in the comments below and explore other articles on our website for more insights into IoT and Raspberry Pi projects.
References:
- Raspberry Pi Foundation
- National Institute of Standards and Technology
- Internet Engineering Task Force