Connecting remote IoT devices using peer-to-peer (P2P) SSH on a Raspberry Pi is a powerful solution for managing and securing your devices. In today's interconnected world, ensuring secure communication between devices is critical to protect sensitive data and maintain privacy. This article will guide you through the best practices for securely connecting remote IoT devices using P2P SSH on a Raspberry Pi, complete with downloadable resources to help you implement these solutions effectively.
As the Internet of Things (IoT) continues to expand, the need for secure and reliable connections becomes increasingly important. Without proper security measures, IoT devices can become vulnerable to cyberattacks, leading to data breaches and other security issues. By leveraging SSH (Secure Shell) and P2P technologies, you can create a secure communication channel between your devices and the Raspberry Pi, ensuring that your network remains protected.
This article will provide an in-depth exploration of the best practices for securely connecting remote IoT devices, including step-by-step instructions, downloadable resources, and expert tips to help you implement these solutions effectively. Whether you're a beginner or an experienced developer, this guide will equip you with the knowledge you need to secure your IoT network.
Read also:Why An Aaacom Credit Card Could Be Your Smart Financial Choice
Table of Contents:
- Introduction to Remote IoT and P2P SSH
- Raspberry Pi Setup for IoT
- Securing SSH Connections
- Overview of P2P SSH
- Best Practices for Secure Connections
- Downloadable Resources
- Troubleshooting Common Issues
- Data Security in IoT Networks
- Performance Optimization Tips
- Conclusion and Next Steps
Introduction to Remote IoT and P2P SSH
The Internet of Things (IoT) has revolutionized the way we interact with technology. Remote IoT devices are becoming increasingly common, from smart home appliances to industrial sensors. To manage these devices effectively, it's essential to establish secure and reliable connections. One of the most effective methods for achieving this is through P2P SSH on a Raspberry Pi.
Remote IoT devices require secure communication channels to ensure data integrity and protect against unauthorized access. P2P SSH provides a secure way to connect devices without relying on traditional server-client architectures, reducing the risk of cyberattacks and improving performance.
By using a Raspberry Pi as the central hub for your IoT network, you can create a scalable and secure infrastructure that supports multiple devices. This section will explore the fundamentals of remote IoT and P2P SSH, laying the groundwork for the rest of the article.
Why Choose Raspberry Pi for IoT?
The Raspberry Pi is a popular choice for IoT projects due to its affordability, versatility, and ease of use. With its small form factor and powerful processing capabilities, the Raspberry Pi can serve as a central hub for managing remote IoT devices. Additionally, its open-source nature allows developers to customize and optimize their setups for specific use cases.
Raspberry Pi Setup for IoT
Setting up a Raspberry Pi for IoT involves several key steps, including installing the operating system, configuring network settings, and enabling SSH. This section will walk you through the process of preparing your Raspberry Pi for secure remote IoT connections.
Read also:Drew Careys Wife Exploring The Life Love And Legacy
Best securely connect remote IoT devices starts with a well-configured Raspberry Pi. Below are the steps to set up your Raspberry Pi:
- Download the Raspberry Pi OS image from the official website.
- Use a tool like Balena Etcher to flash the image onto an SD card.
- Insert the SD card into your Raspberry Pi and power it on.
- Connect to your Wi-Fi network or Ethernet.
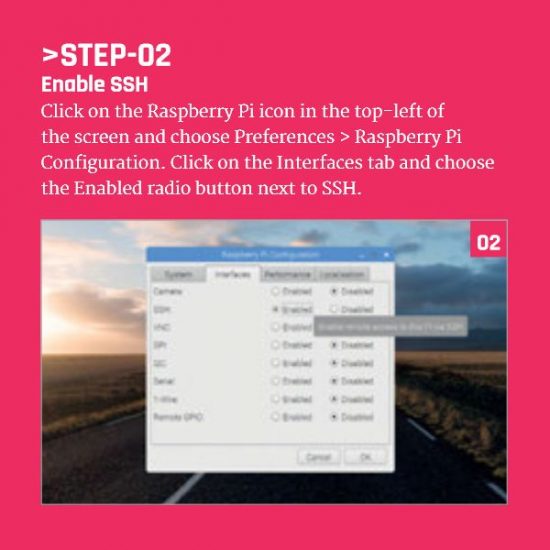
- Enable SSH in the Raspberry Pi configuration settings.
Once your Raspberry Pi is set up, you can begin configuring it for secure remote IoT connections.
Configuring Network Settings
Proper network configuration is crucial for ensuring secure communication between your Raspberry Pi and remote IoT devices. This includes setting up static IP addresses, configuring firewalls, and enabling secure authentication methods.
Securing SSH Connections
SSH (Secure Shell) is a protocol used for secure communication between devices. When connecting remote IoT devices, it's essential to secure your SSH connections to prevent unauthorized access and data breaches. Below are some best practices for securing SSH connections:
- Disable password authentication and use SSH keys instead.
- Change the default SSH port to a non-standard port.
- Limit SSH access to specific IP addresses or networks.
- Enable two-factor authentication (2FA) for added security.
By implementing these measures, you can significantly enhance the security of your SSH connections and protect your IoT network from potential threats.
Overview of P2P SSH
Peer-to-peer (P2P) SSH allows devices to connect directly without relying on a central server. This approach offers several advantages, including improved security, reduced latency, and increased scalability. In this section, we'll explore the basics of P2P SSH and how it can be applied to remote IoT networks.
P2P SSH is particularly useful for IoT applications where devices need to communicate securely and efficiently. By eliminating the need for a central server, P2P SSH reduces the risk of single points of failure and makes it more difficult for attackers to compromise the network.
Benefits of P2P SSH
Some of the key benefits of using P2P SSH for remote IoT connections include:
- Enhanced security through direct device-to-device communication.
- Improved performance with reduced latency.
- Scalability to accommodate a growing number of devices.
Best Practices for Secure Connections
To ensure the best possible security for your remote IoT network, it's important to follow established best practices. This section will provide expert tips and guidelines for securing your connections and protecting your data.
Best securely connect practices include regular updates, monitoring network activity, and using encryption protocols. Below are some additional tips:
- Regularly update your Raspberry Pi and IoT devices with the latest firmware and security patches.
- Monitor network traffic for suspicious activity and potential threats.
- Encrypt sensitive data using strong encryption algorithms.
By following these best practices, you can create a robust and secure IoT network that protects your devices and data.
Monitoring Network Activity
Effective network monitoring is essential for detecting and responding to potential security threats. Use tools like fail2ban and iptables to monitor and control access to your Raspberry Pi and IoT devices.
Downloadable Resources
To help you implement the solutions discussed in this article, we've compiled a list of downloadable resources. These resources include configuration files, scripts, and documentation to assist you in setting up and securing your remote IoT network.
These resources are designed to simplify the process of securing your remote IoT connections and provide a solid foundation for building a secure IoT network.
Troubleshooting Common Issues
Even with the best planning and preparation, issues can arise when setting up and securing remote IoT connections. This section will address common problems and provide solutions to help you troubleshoot and resolve them.
Some common issues include:
- SSH connection failures due to incorrect configuration.
- Network connectivity problems caused by firewall restrictions.
- Device authentication errors resulting from mismatched keys.
By understanding these issues and their solutions, you can quickly resolve problems and maintain a secure IoT network.
SSH Connection Troubleshooting
If you encounter issues with SSH connections, check the following:
- Verify that SSH is enabled on your Raspberry Pi.
- Ensure that the correct SSH keys are installed on both devices.
- Check firewall settings to confirm that SSH traffic is allowed.
Data Security in IoT Networks
Data security is a critical component of any IoT network. With the increasing amount of sensitive data being transmitted between devices, it's essential to implement robust security measures to protect against unauthorized access and data breaches.
Data security in IoT networks involves encryption, access control, and regular audits. Below are some strategies for enhancing data security:
- Encrypt all data transmitted between devices using strong encryption protocols.
- Implement role-based access control to restrict access to sensitive data.
- Conduct regular security audits to identify and address potential vulnerabilities.
By prioritizing data security, you can ensure the integrity and confidentiality of your IoT network.
Performance Optimization Tips
Optimizing the performance of your remote IoT network is essential for ensuring reliable and efficient communication between devices. This section will provide tips for improving the performance of your Raspberry Pi and IoT devices.
Performance optimization involves optimizing network settings, reducing latency, and improving resource utilization. Below are some strategies for enhancing performance:
- Optimize network settings to reduce latency and improve throughput.
- Use lightweight protocols to minimize resource usage on IoT devices.
- Regularly monitor and analyze network performance to identify bottlenecks.
By following these tips, you can create a high-performance IoT network that meets the needs of your applications.
Conclusion and Next Steps
In conclusion, securely connecting remote IoT devices using P2P SSH on a Raspberry Pi is a powerful solution for managing and protecting your IoT network. By following the best practices outlined in this article and utilizing the provided downloadable resources, you can create a secure and efficient IoT network that meets the demands of modern applications.
We encourage you to take the next steps by implementing these solutions in your own projects. Leave a comment below to share your experiences and ask questions. Additionally, feel free to share this article with others who may find it useful. Together, we can build a safer and more connected world through secure IoT technology.
References:
- Raspberry Pi Official Website
- SSH.com - Secure Shell Resources
- NIST - National Institute of Standards and Technology