In today's digital age, securely connect remote IoT P2P SSH Raspberry Pi free has become an essential skill for tech enthusiasts and professionals alike. As more devices become interconnected, ensuring secure communication between them is critical to protecting sensitive data. This guide will provide you with all the necessary information to set up a secure connection between IoT devices using Raspberry Pi through SSH.
Whether you're a hobbyist working on home automation projects or a professional managing industrial IoT systems, understanding how to establish secure connections is crucial. This article aims to simplify the process and offer practical advice to help you achieve this goal efficiently.
Our focus will be on using Raspberry Pi as the central hub for your IoT network, leveraging SSH (Secure Shell) for secure communication. We'll explore various methods to set up peer-to-peer (P2P) connections, ensuring your devices remain protected from unauthorized access.
Read also:Alexis Maas The Rising Star In The Fashion Industry
Table of Contents
- Introduction to SSH and Its Importance
- Overview of Raspberry Pi for IoT Projects
- Setting Up Raspberry Pi for IoT
- Securing IoT Connections with SSH
- Setting Up Remote Access
- Establishing P2P Connections
- Best Practices for Secure Connections
- Troubleshooting Common Issues
- Additional Security Tips
- Conclusion and Next Steps
Introduction to SSH and Its Importance
SSH (Secure Shell) is a cryptographic network protocol that ensures secure communication between devices over an unsecured network. It is widely used for remote administration and file transfer. When you securely connect remote IoT P2P SSH Raspberry Pi free, SSH plays a pivotal role in safeguarding your data and network.
SSH offers several advantages, including:
- Encryption of data during transmission
- Authentication of users and devices
- Protection against eavesdropping and data tampering
For IoT projects, SSH provides a reliable method to manage and monitor devices remotely, ensuring that your network remains secure and functional.
Variations of SSH Protocols
There are different versions of the SSH protocol, with SSH-2 being the most commonly used today. It offers enhanced security features compared to its predecessor, SSH-1. Understanding the differences between these versions can help you choose the best option for your IoT setup.
Overview of Raspberry Pi for IoT Projects
Raspberry Pi is a versatile, credit-card-sized computer that has gained immense popularity among tech enthusiasts and professionals alike. Its affordability, flexibility, and ease of use make it an ideal choice for IoT projects.
When you securely connect remote IoT P2P SSH Raspberry Pi free, Raspberry Pi acts as the central hub, enabling seamless communication between devices. Its compatibility with various operating systems and programming languages makes it a powerful tool for building IoT networks.
Read also:How Did Rand Paul Make His Money A Comprehensive Guide To His Wealth And Influence
Key Features of Raspberry Pi
- Compact size and low power consumption
- Support for multiple operating systems, including Linux
- Compatibility with a wide range of sensors and actuators
- Easy integration with cloud platforms
Setting Up Raspberry Pi for IoT
Before you can securely connect remote IoT P2P SSH Raspberry Pi free, you need to set up your Raspberry Pi properly. This involves installing the operating system, configuring network settings, and ensuring all necessary software is installed.
Step-by-Step Guide to Setup
Here’s a step-by-step guide to help you get started:
- Download and install the latest version of Raspberry Pi OS.
- Connect your Raspberry Pi to a monitor, keyboard, and mouse.
- Configure Wi-Fi or Ethernet settings for network connectivity.
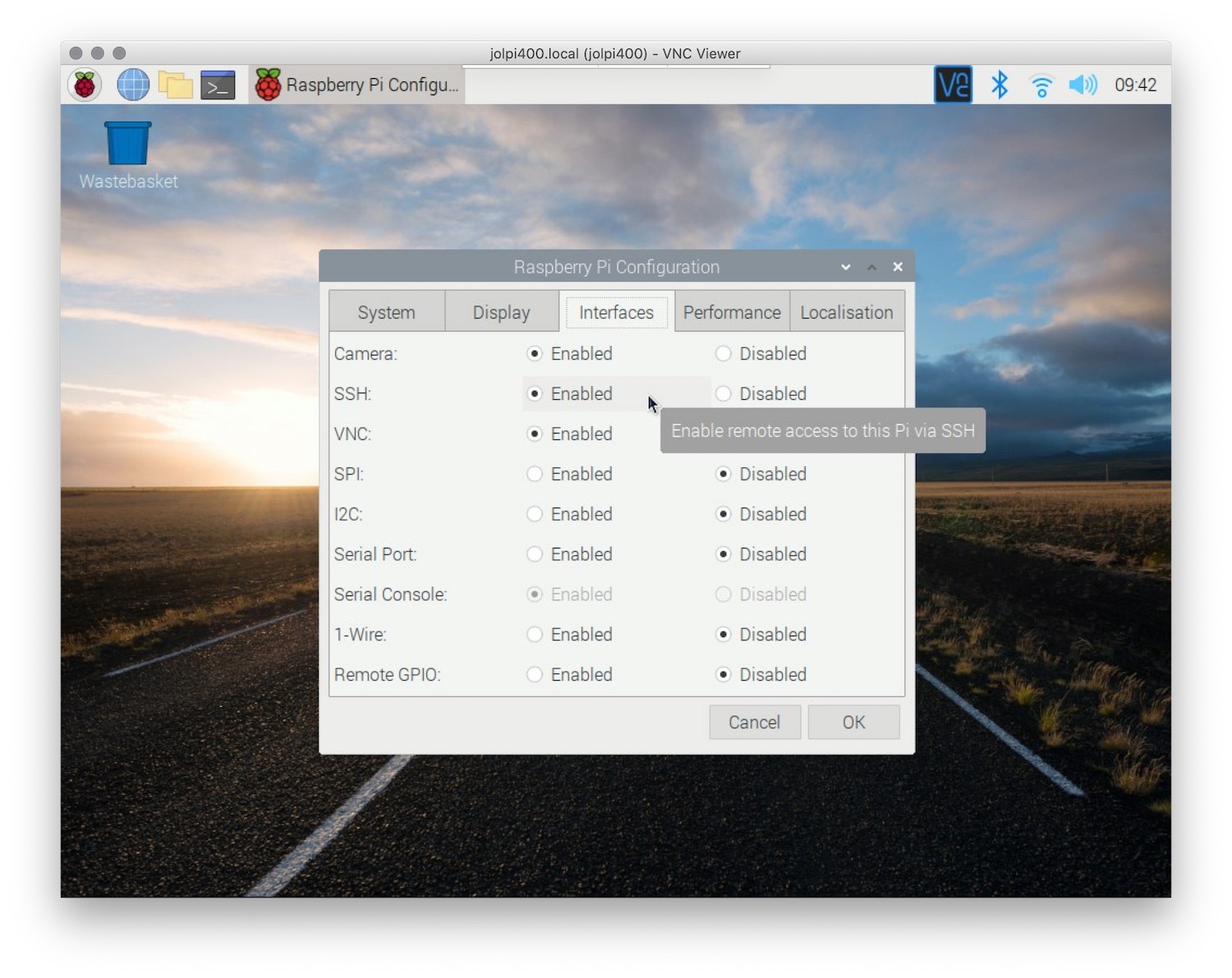
- Install and enable SSH by running the command
sudo raspi-config.
Securing IoT Connections with SSH
Securing your IoT connections is paramount to protecting your network and devices. By using SSH, you can encrypt data transmissions and authenticate users, ensuring that only authorized parties can access your network.
When you securely connect remote IoT P2P SSH Raspberry Pi free, consider implementing additional security measures such as:
- Using strong, unique passwords
- Enabling two-factor authentication
- Regularly updating software and firmware
SSH Key Authentication
SSH key authentication is a more secure alternative to password-based authentication. It involves generating a pair of public and private keys, which are used to authenticate users without the need for passwords.
Setting Up Remote Access
Remote access is essential for managing IoT devices from anywhere in the world. By securely connect remote IoT P2P SSH Raspberry Pi free, you can monitor and control your devices without being physically present.
To set up remote access, follow these steps:
- Enable SSH on your Raspberry Pi.
- Configure port forwarding on your router.
- Use a dynamic DNS service to assign a domain name to your Raspberry Pi.
Tools for Remote Access
There are several tools available to facilitate remote access, including:
- Putty (for Windows)
- Terminal (for macOS and Linux)
- Mobile apps like JuiceSSH
Establishing P2P Connections
Peer-to-peer (P2P) connections allow devices to communicate directly with each other without relying on a central server. This can enhance the efficiency and reliability of your IoT network.
When you securely connect remote IoT P2P SSH Raspberry Pi free, consider using P2P protocols such as WebRTC or ZeroTier to establish direct connections between devices.
Advantages of P2P Connections
- Reduced latency and improved performance
- Lower dependency on centralized servers
- Enhanced privacy and security
Best Practices for Secure Connections
Implementing best practices is crucial to maintaining the security of your IoT network. Here are some tips to help you securely connect remote IoT P2P SSH Raspberry Pi free:
- Regularly update your Raspberry Pi's operating system and software.
- Use firewalls to restrict unauthorized access.
- Monitor network activity for suspicious behavior.
Regular Security Audits
Conducting regular security audits can help identify vulnerabilities in your network and ensure that all security measures are functioning correctly.
Troubleshooting Common Issues
Even with proper setup and configuration, issues may arise. Here are some common problems and their solutions:
- SSH connection fails: Check network settings and ensure SSH is enabled.
- Device not responding: Restart the Raspberry Pi and verify connections.
- Slow performance: Optimize code and reduce unnecessary processes.
Resources for Further Assistance
For additional support, consider consulting online forums, documentation, or professional services.
Additional Security Tips
Here are some additional tips to enhance the security of your IoT network:
- Use intrusion detection systems to monitor for threats.
- Implement data encryption for sensitive information.
- Limit access to critical systems to trusted users only.
Staying Informed
Stay updated with the latest security trends and technologies to ensure your IoT network remains protected.
Conclusion and Next Steps
In conclusion, securely connect remote IoT P2P SSH Raspberry Pi free is a vital skill for anyone involved in IoT projects. By following the guidelines and best practices outlined in this article, you can establish a secure and efficient network that meets your needs.
We encourage you to take the next step by implementing what you've learned and experimenting with different configurations to optimize your setup. Don't forget to share your experiences and insights with the community, and feel free to explore other articles on our site for more valuable information.
Call to Action: Let us know in the comments below how this guide has helped you, and consider subscribing to our newsletter for more updates and tips!