As technology continues to evolve, the Internet of Things (IoT) has emerged as a revolutionary force, connecting devices in ways previously unimaginable. One of the most critical aspects of IoT is ensuring secure communication between devices, especially when connecting remotely. Securely connecting remote IoT devices through peer-to-peer (P2P) SSH on Windows 10 is not only essential for data integrity but also for safeguarding against potential cyber threats.
With the increasing number of IoT devices being deployed globally, the need for robust security measures has never been more pressing. This article will explore the best practices for establishing secure remote connections using P2P SSH on Windows 10, ensuring your IoT devices remain protected. Whether you're a developer, system administrator, or tech enthusiast, this guide will provide valuable insights to help you achieve secure IoT connectivity.
By the end of this article, you'll have a thorough understanding of the tools, techniques, and configurations required to securely connect IoT devices using P2P SSH on Windows 10. Let's dive into the details and explore how you can safeguard your IoT ecosystem effectively.
Read also:How Tall Is Jessica Tarlov Discover The Height And More About This Rising Star
Table of Contents
- Introduction to IoT Security
- Understanding P2P SSH for IoT
- Setting Up SSH on Windows 10
- Securing Remote Access
- Implementing Strong Encryption
- Configuring Firewalls for IoT Devices
- Best Practices for IoT Security
- Troubleshooting Common Issues
- Recommended Tools and Software
- The Future of IoT Security
Introduction to IoT Security
IoT security is a critical aspect of modern technology, especially when it comes to protecting sensitive data and ensuring device integrity. With billions of IoT devices connected worldwide, securing these devices from unauthorized access is paramount. The keyword "securely connect remote IoT P2P SSH Windows 10" highlights the importance of establishing a secure connection between IoT devices using peer-to-peer SSH on Windows 10.
IoT devices are often deployed in remote locations, making them vulnerable to cyberattacks. Hackers can exploit weak security protocols to gain unauthorized access, leading to data breaches and potential system failures. To mitigate these risks, it's essential to implement robust security measures, such as SSH, which provides encrypted communication channels between devices.
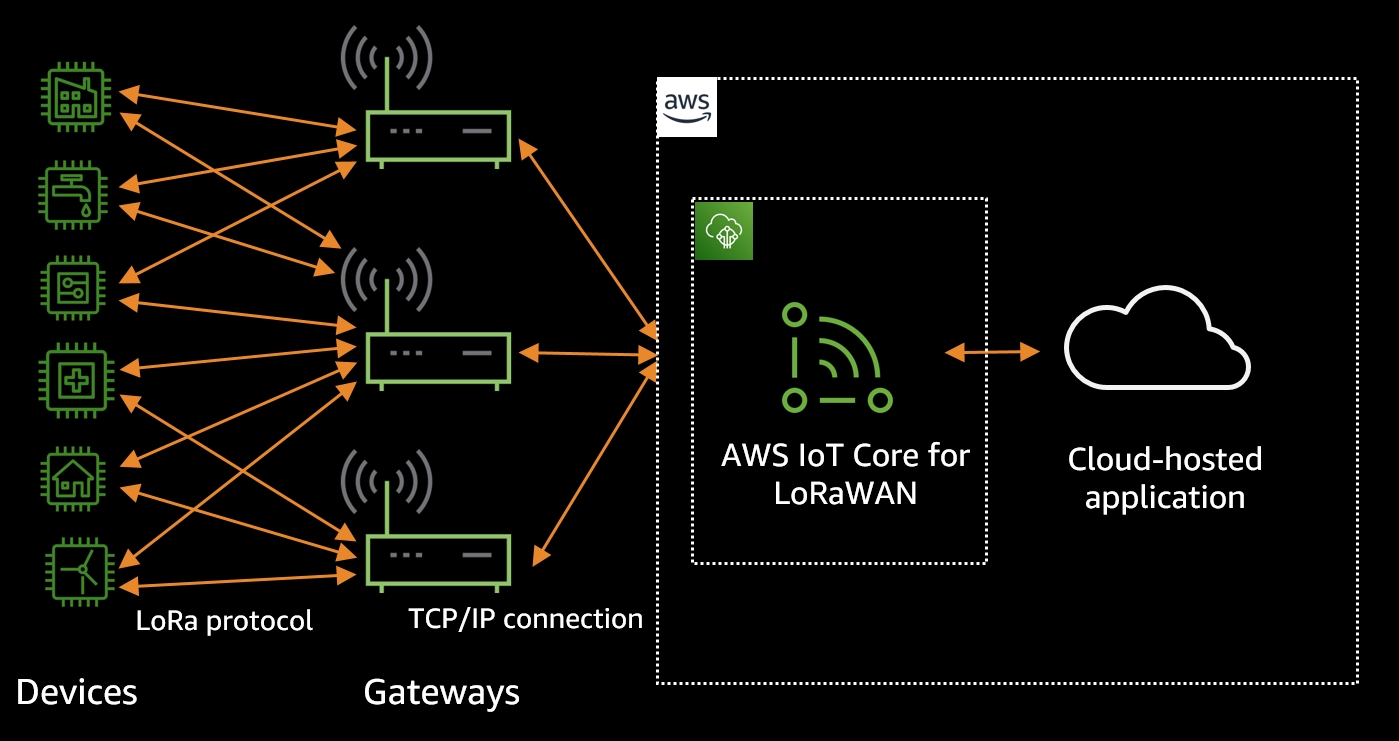
SSH, or Secure Shell, is a cryptographic network protocol that enables secure communication over unsecured networks. When combined with P2P technology, SSH ensures that IoT devices can communicate directly without relying on centralized servers, reducing latency and enhancing security.
Understanding P2P SSH for IoT
What is P2P SSH?
P2P SSH refers to the use of Secure Shell protocols in a peer-to-peer network environment. This approach allows IoT devices to establish direct connections without intermediaries, ensuring faster and more secure communication. By leveraging P2P SSH, organizations can reduce dependency on third-party servers, which can be potential points of failure or attack.
Benefits of P2P SSH
- Enhanced Security: Direct connections minimize the risk of data interception.
- Reduced Latency: P2P connections are faster since they bypass centralized servers.
- Scalability: P2P SSH can handle large numbers of devices without compromising performance.
P2P SSH is particularly useful for IoT devices that require real-time communication, such as industrial sensors, smart home appliances, and healthcare devices. By implementing this technology, organizations can ensure that their IoT ecosystems remain secure and efficient.
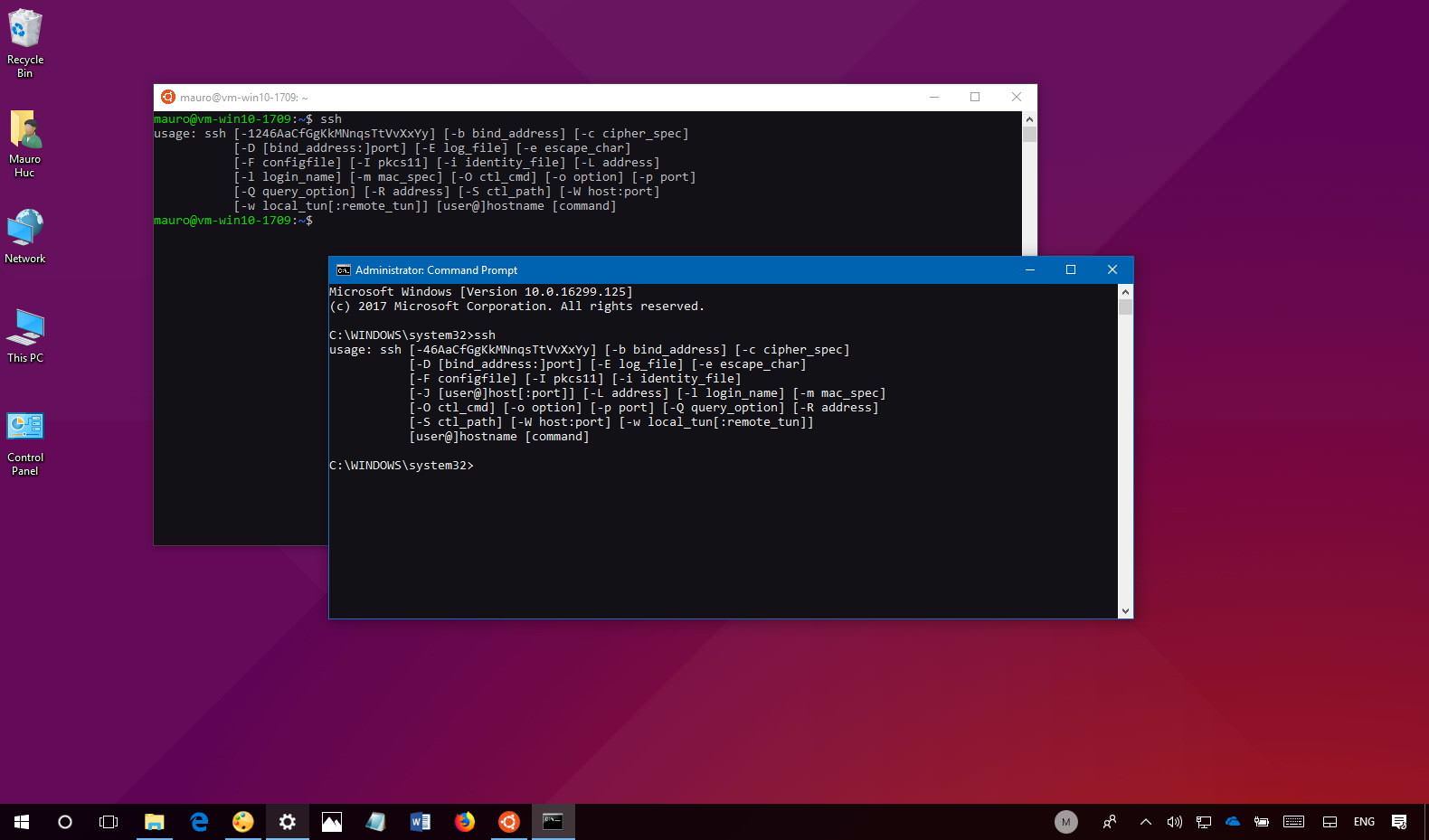
Setting Up SSH on Windows 10
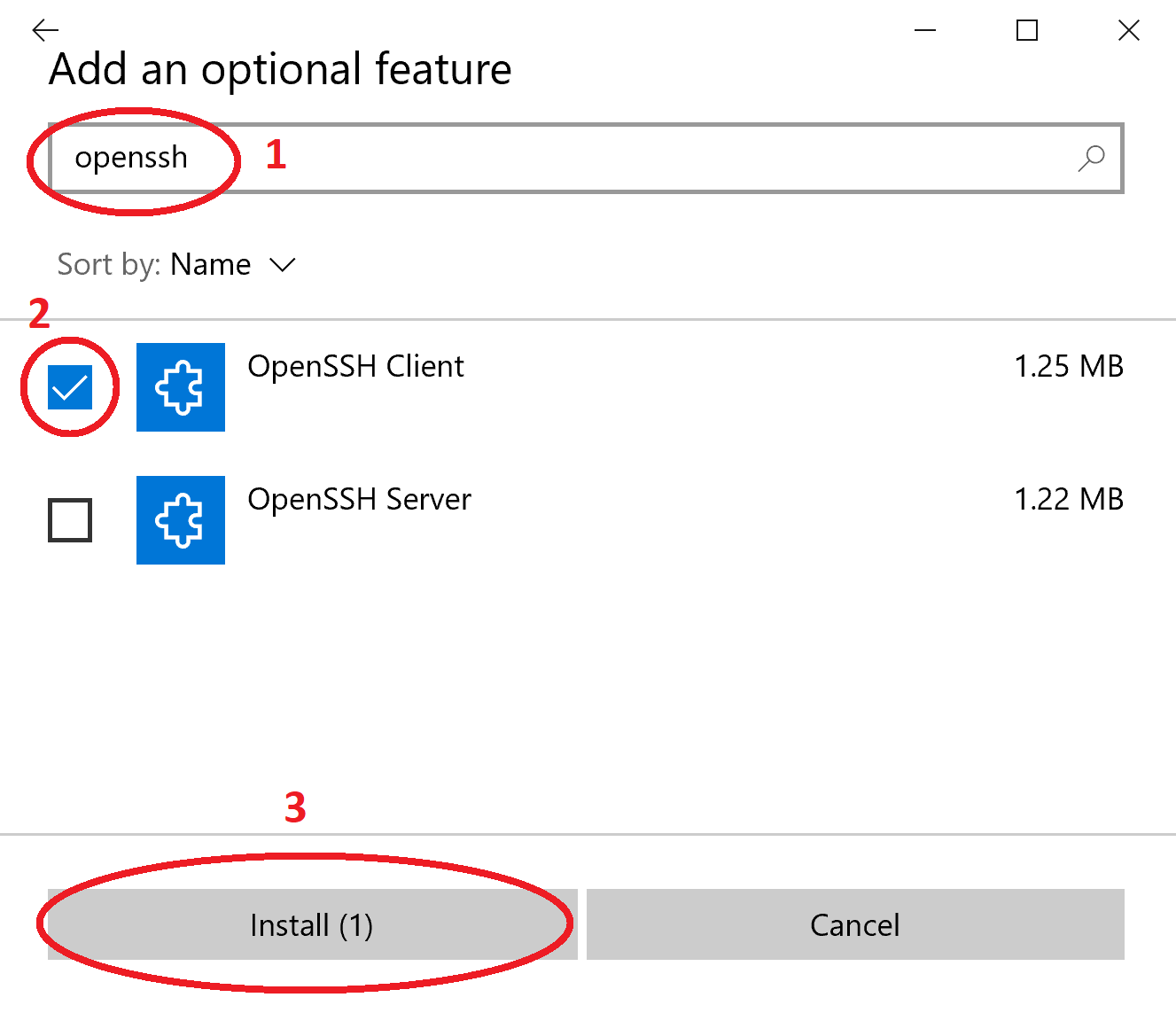
Windows 10 provides built-in support for SSH, making it easier to configure secure connections for IoT devices. To set up SSH on Windows 10, follow these steps:
Read also:Spell Anniversary Celebrating Love And Togetherness
- Enable the OpenSSH Client and Server features in Windows Settings.
- Generate SSH keys using the ssh-keygen command.
- Configure the SSH server by editing the sshd_config file.
- Test the connection using the ssh command.
By properly configuring SSH on Windows 10, you can establish secure connections with IoT devices, ensuring that all communication is encrypted and protected from unauthorized access.
Securing Remote Access
Why Secure Remote Access Matters
Remote access is a fundamental requirement for managing IoT devices, but it also poses significant security risks. Hackers can exploit unsecured remote connections to gain unauthorized access to sensitive data and systems. To mitigate these risks, it's crucial to implement secure remote access protocols, such as P2P SSH.
Steps to Secure Remote Access
- Use strong passwords and two-factor authentication.
- Limit SSH access to specific IP addresses or subnets.
- Regularly update SSH server software and configurations.
- Monitor and log all SSH connection attempts for suspicious activity.
By following these best practices, you can ensure that your remote IoT connections remain secure and protected from potential threats.
Implementing Strong Encryption
Encryption is a key component of secure IoT communication, ensuring that data transmitted between devices remains confidential and tamper-proof. When using P2P SSH, it's essential to implement strong encryption protocols to protect sensitive information.
Modern encryption algorithms, such as AES-256 and RSA-2048, provide robust security for IoT devices. By configuring SSH to use these algorithms, you can ensure that all data transmitted between devices is encrypted and protected from unauthorized access.
Configuring Firewalls for IoT Devices
Why Firewalls Are Important
Firewalls play a critical role in securing IoT devices by controlling incoming and outgoing network traffic. By properly configuring firewalls, you can block unauthorized access attempts and protect your IoT devices from potential cyberattacks.
Steps to Configure Firewalls
- Enable the built-in Windows Firewall or use a third-party firewall solution.
- Create rules to allow only necessary SSH traffic on specific ports.
- Block all other incoming and outgoing traffic to minimize risks.
- Regularly review and update firewall rules to adapt to changing security requirements.
By configuring firewalls effectively, you can enhance the security of your IoT ecosystem and protect against potential threats.
Best Practices for IoT Security
To ensure the security of your IoT devices, it's essential to follow best practices that address potential vulnerabilities and risks. Here are some key recommendations:
- Regularly update firmware and software for all IoT devices.
- Use strong, unique passwords for each device and enable two-factor authentication.
- Segment IoT devices on separate networks to limit potential attack surfaces.
- Monitor device activity and log all connections for suspicious behavior.
- Implement secure communication protocols, such as P2P SSH, for all IoT devices.
By adhering to these best practices, you can significantly enhance the security of your IoT ecosystem and protect against potential threats.
Troubleshooting Common Issues
When setting up secure IoT connections using P2P SSH on Windows 10, you may encounter various issues that can affect connectivity and security. Here are some common problems and their solutions:
- Connection Errors: Check SSH server configurations and ensure that firewalls allow necessary traffic.
- Authentication Failures: Verify SSH keys and ensure that passwords meet security requirements.
- Performance Issues: Optimize SSH configurations and reduce unnecessary network traffic.
By addressing these issues promptly, you can ensure that your IoT devices remain securely connected and operational.
Recommended Tools and Software
Several tools and software solutions can help you implement and manage secure IoT connections using P2P SSH on Windows 10. Some of the most popular options include:
- OpenSSH: A widely used open-source SSH implementation for Windows.
- Wireshark: A network protocol analyzer for monitoring and troubleshooting SSH connections.
- Putty: A popular SSH client for Windows that simplifies remote access configurations.
By utilizing these tools, you can streamline the process of setting up and managing secure IoT connections, ensuring optimal performance and security.
The Future of IoT Security
As IoT technology continues to evolve, the need for robust security measures will only increase. Emerging technologies, such as quantum computing and blockchain, are expected to play a significant role in enhancing IoT security in the future.
Quantum computing promises to revolutionize encryption algorithms, providing unprecedented levels of security for IoT devices. Meanwhile, blockchain technology offers decentralized solutions for secure data storage and communication, reducing the risk of single points of failure.
By staying informed about these advancements and adapting to changing security requirements, organizations can ensure that their IoT ecosystems remain secure and efficient in the years to come.
Conclusion
In conclusion, securely connecting remote IoT devices through P2P SSH on Windows 10 is a critical aspect of modern IoT security. By following the best practices outlined in this article, you can ensure that your IoT devices remain protected from potential cyber threats and maintain optimal performance.
We encourage you to implement the recommendations discussed in this guide and explore the recommended tools and software to enhance your IoT security. Don't forget to share your thoughts and experiences in the comments section below, and feel free to explore other articles on our site for more insights into IoT and cybersecurity.