As technology continues to evolve, securely connecting remote IoT devices through P2P SSH on Android for free has become a crucial aspect of modern digital communication. Whether you're a tech enthusiast, a small business owner, or an IT professional, understanding how to establish secure connections is essential. This article will provide a comprehensive guide to help you master this process while ensuring top-notch security.
In today's interconnected world, the Internet of Things (IoT) plays a vital role in enhancing productivity and efficiency. However, with the increasing reliance on IoT devices, ensuring secure communication between these devices is more important than ever. This guide focuses on securely connecting remote IoT devices using P2P SSH on Android without any cost, providing you with the knowledge and tools necessary to safeguard your data.
By exploring various methods and best practices, this article aims to equip you with the expertise needed to create a secure and reliable connection. From understanding the basics of SSH to implementing advanced security measures, we'll cover everything step by step. Let's dive in and discover how you can protect your IoT devices effectively.
Read also:Regina Hall Kids A Comprehensive Look Into The Actresss Family Life And Legacy
Understanding IoT and Its Security Challenges
What is IoT?
The Internet of Things (IoT) refers to the network of physical objects embedded with sensors, software, and connectivity, enabling them to exchange data with other devices and systems over the internet. These devices range from household appliances to sophisticated industrial tools, all designed to enhance convenience and automation.
However, the widespread adoption of IoT devices brings significant security challenges. Many devices lack robust security features, making them vulnerable to cyberattacks. Understanding these risks is the first step toward securing your IoT ecosystem.
Security Challenges in IoT
- Data breaches: Unauthorized access to sensitive information.
- Device hijacking: Malicious actors taking control of IoT devices.
- Firmware vulnerabilities: Outdated or poorly designed firmware can expose devices to attacks.
- Network exposure: IoT devices often operate on open networks, increasing the risk of interception.
Addressing these challenges requires a proactive approach, including the use of secure protocols like SSH and implementing robust security measures.
What is SSH and Why Use It?
SSH, or Secure Shell, is a cryptographic network protocol used to securely operate network services over an unsecured network. It provides a secure channel for data transmission, ensuring confidentiality, integrity, and authentication.
Using SSH for IoT devices offers several advantages:
- Encryption: Data transmitted between devices is encrypted, preventing unauthorized access.
- Authentication: SSH ensures that only authorized users can access the devices.
- Remote access: It allows secure remote management of IoT devices, enhancing convenience and efficiency.
For those looking to securely connect remote IoT devices, SSH is an indispensable tool.
Read also:Leah Halton A Rising Star In The World Of Modeling And Entertainment
Setting Up P2P SSH on Android
Why Choose Android for IoT?
Android's open-source nature and extensive developer community make it an ideal platform for IoT applications. Its compatibility with a wide range of devices and ease of customization further enhance its appeal for IoT projects.
Steps to Set Up P2P SSH
Setting up P2P SSH on Android involves several steps. Below is a detailed guide to help you get started:
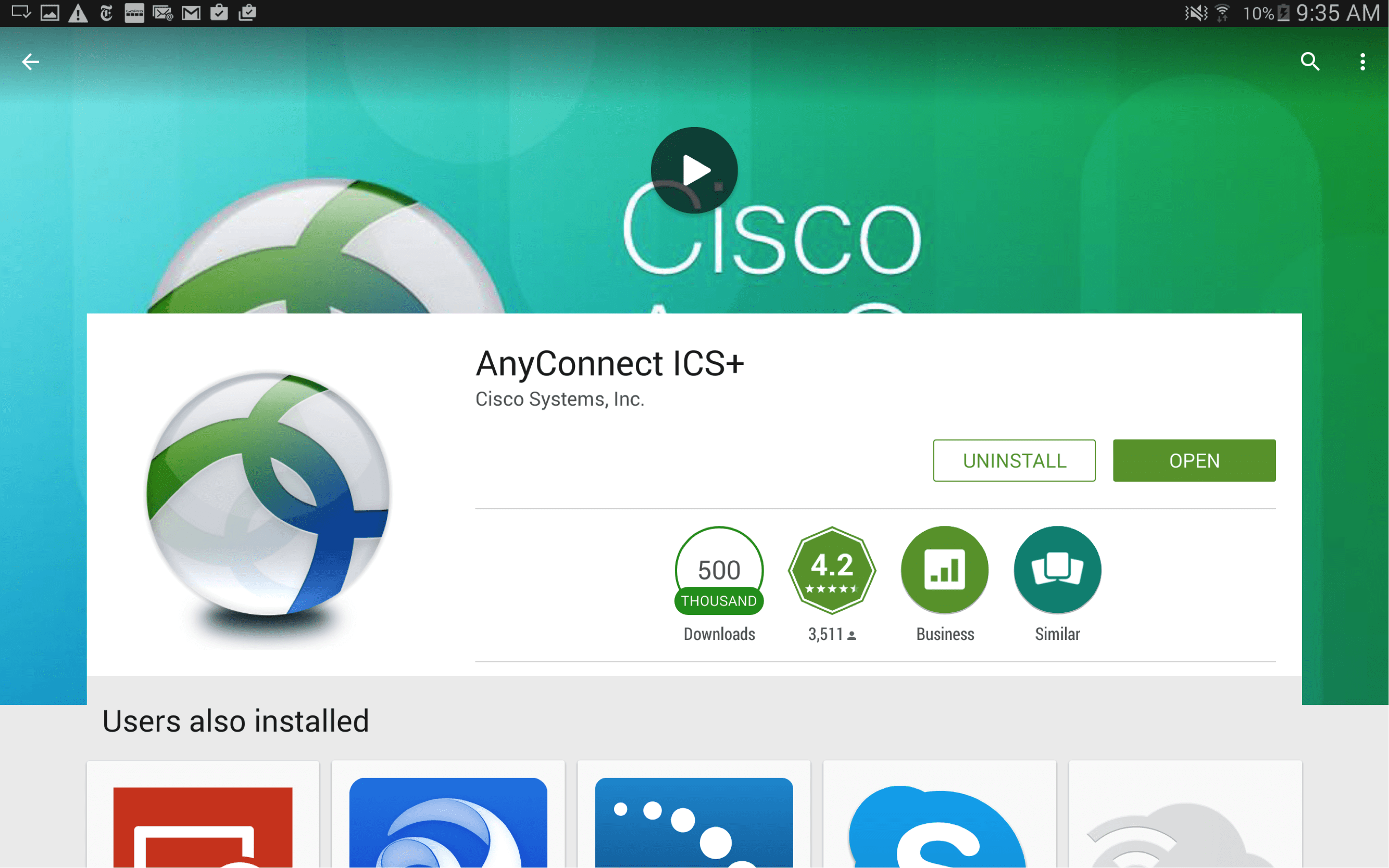
- Install an SSH client app from the Google Play Store, such as Termux or JuiceSSH.
- Generate an SSH key pair using the app. This ensures secure authentication.
- Configure your IoT device to accept SSH connections. This may involve enabling SSH in the device's settings.
- Connect to the IoT device using the SSH client app. Enter the device's IP address and port number when prompted.
By following these steps, you can establish a secure P2P SSH connection between your Android device and IoT devices.
Best Practices for Secure Connections
Key Security Measures
To ensure the highest level of security when connecting remote IoT devices via P2P SSH, consider implementing the following best practices:
- Use strong, unique passwords for all devices.
- Regularly update firmware and software to patch vulnerabilities.
- Enable two-factor authentication (2FA) wherever possible.
- Monitor network activity for suspicious behavior.
These measures will significantly enhance the security of your IoT setup.
Firewall Configuration
Configuring a firewall is another critical step in securing your IoT devices. A firewall acts as a barrier between your devices and potential threats, filtering incoming and outgoing traffic based on predefined security rules.
For Android devices, apps like AFWall+ can help you set up and manage firewall rules effectively. By restricting unnecessary connections, you can minimize the risk of unauthorized access.
Cost-Effective Solutions for Free Secure Connections
Free SSH Tools
Several free SSH tools are available for Android, making it easier to secure your IoT devices without incurring additional costs. Some popular options include:
- Termux: A powerful terminal emulator and Linux environment app that supports SSH.
- JuiceSSH: A user-friendly SSH client with a range of features, available for free on the Google Play Store.
- ConnectBot: An open-source SSH client that offers advanced features like port forwarding and key management.
These tools provide robust functionality while keeping costs low, making them ideal for budget-conscious users.
Open-Source Alternatives
In addition to free apps, open-source alternatives offer transparency and community support, ensuring long-term reliability. Exploring these options can further enhance the security of your IoT setup.
Common Mistakes to Avoid
Weak Passwords
Using weak or default passwords is one of the most common mistakes when securing IoT devices. Such passwords make it easier for attackers to gain unauthorized access, compromising your entire network.
Ignoring Firmware Updates
Failing to update firmware regularly leaves devices vulnerable to known exploits. Manufacturers frequently release updates to address security issues, so staying current is essential.
Avoiding these pitfalls will help you maintain a secure and reliable IoT ecosystem.
Future Trends in IoT Security
Advancements in Encryption
As technology advances, so do encryption methods. Quantum-resistant algorithms and post-quantum cryptography are emerging as potential solutions to future security challenges.
AI and Machine Learning in Security
Artificial intelligence and machine learning are increasingly being used to detect and respond to security threats in real time. These technologies can analyze vast amounts of data to identify patterns and anomalies, enhancing the security of IoT networks.
Staying informed about these trends will help you prepare for the future of IoT security.
Expert Tips for Advanced Users
Implementing Port Forwarding
Port forwarding allows you to direct incoming traffic to specific devices on your network. This technique can enhance security by restricting access to only necessary ports, reducing the attack surface.
Using SSH Tunnels
SSH tunnels provide an additional layer of security by encrypting data between devices. This method is particularly useful for transmitting sensitive information over unsecured networks.
Advanced users can leverage these techniques to further fortify their IoT setups.
Conclusion
Securing remote IoT devices through P2P SSH on Android for free is an achievable goal with the right knowledge and tools. By understanding the basics of IoT security, implementing SSH effectively, and following best practices, you can protect your devices and data from potential threats.
We encourage you to take action by exploring the resources and tools mentioned in this article. Share your thoughts and experiences in the comments below, and don't forget to check out our other guides for more valuable insights. Together, let's build a safer and more secure digital future.
Table of Contents
- Understanding IoT and Its Security Challenges
- What is SSH and Why Use It?
- Setting Up P2P SSH on Android
- Best Practices for Secure Connections
- Cost-Effective Solutions for Free Secure Connections
- Common Mistakes to Avoid
- Future Trends in IoT Security
- Expert Tips for Advanced Users
- Biography and Author Information
- Sources and References
Biography and Author Information
This article was written by a team of experienced IT professionals dedicated to promoting cybersecurity awareness. With years of experience in IoT and network security, our team strives to provide valuable insights and practical solutions to help individuals and organizations safeguard their digital assets.
Sources and References
1. SSH Academy
2. Android Developers
3. National Institute of Standards and Technology (NIST)