In today's interconnected world, securely connect remote IoT P2P SSH has become an essential skill for anyone working with Internet of Things (IoT) devices. Whether you're a developer, network administrator, or simply someone interested in secure communication, understanding how to establish a secure connection is crucial. This guide will provide you with all the information you need to download and use free tools for secure remote IoT connections.
As technology continues to evolve, so do the methods for ensuring secure communication between devices. IoT devices are increasingly being used in homes, businesses, and industries, making it more important than ever to protect them from unauthorized access and cyber threats. By learning how to securely connect remote IoT devices using P2P SSH, you can safeguard sensitive data and ensure the smooth operation of your network.
This article will cover everything from the basics of IoT security to advanced techniques for establishing secure connections. Whether you're a beginner or an experienced professional, you'll find valuable insights and practical advice to enhance your knowledge and skills in this area.
Read also:Alex Kleyner National Debt Relief Your Ultimate Guide To Financial Freedom
Table of Contents
- Introduction to IoT Security
- Understanding P2P SSH
- Why Secure Remote Connections Matter
- Tools for Securely Connecting Remote IoT
- Step-by-Step Guide to Secure Connections
- Best Practices for Remote IoT Security
- Common SSH Pitfalls to Avoid
- Free SSH Tools for Remote IoT
- Case Studies of Successful Implementation
- Conclusion and Next Steps
Introduction to IoT Security
IoT security is a critical component of modern technology infrastructure. With billions of devices connected to the internet, ensuring their security is no longer an option but a necessity. Securely connect remote IoT P2P SSH is one of the most effective ways to protect these devices from unauthorized access.
IoT devices are vulnerable to various types of cyber threats, including hacking, data breaches, and malware attacks. By implementing robust security measures, you can minimize these risks and ensure the integrity of your network. P2P SSH offers a secure method for remote access, allowing you to manage and monitor your IoT devices without compromising their security.
Why IoT Security is Important
- Prevents unauthorized access to sensitive data.
- Protects devices from cyberattacks.
- Ensures the smooth operation of networks and systems.
- Complies with industry regulations and standards.
Understanding P2P SSH
Peer-to-peer (P2P) SSH is a secure communication protocol that allows devices to connect directly without relying on a central server. This method provides several advantages, including enhanced security, reduced latency, and improved reliability. By securely connect remote IoT P2P SSH, you can establish a direct connection between devices, ensuring that data is transmitted securely and efficiently.
How P2P SSH Works
P2P SSH operates by creating a secure tunnel between two devices, allowing them to communicate directly. This tunnel encrypts all data transmitted between the devices, making it virtually impossible for hackers to intercept or tamper with the information. The protocol also includes authentication mechanisms to ensure that only authorized devices can connect to the network.
Why Secure Remote Connections Matter
In today's digital age, remote connections have become an integral part of our daily lives. Whether you're working from home, managing a business, or controlling smart home devices, secure remote connections are essential for protecting your data and ensuring the smooth operation of your systems. By securely connect remote IoT P2P SSH, you can enjoy the benefits of remote access without compromising your security.
Benefits of Secure Remote Connections
- Enhanced data protection.
- Improved network performance.
- Increased flexibility and convenience.
- Reduced risk of cyberattacks.
Tools for Securely Connecting Remote IoT
There are several tools available for securely connecting remote IoT devices using P2P SSH. These tools range from free, open-source solutions to commercial products with advanced features. When choosing a tool, it's important to consider factors such as ease of use, compatibility, and security features.
Read also:The Skinniest Person Ever Exploring The Extraordinary Story
Popular SSH Tools for IoT
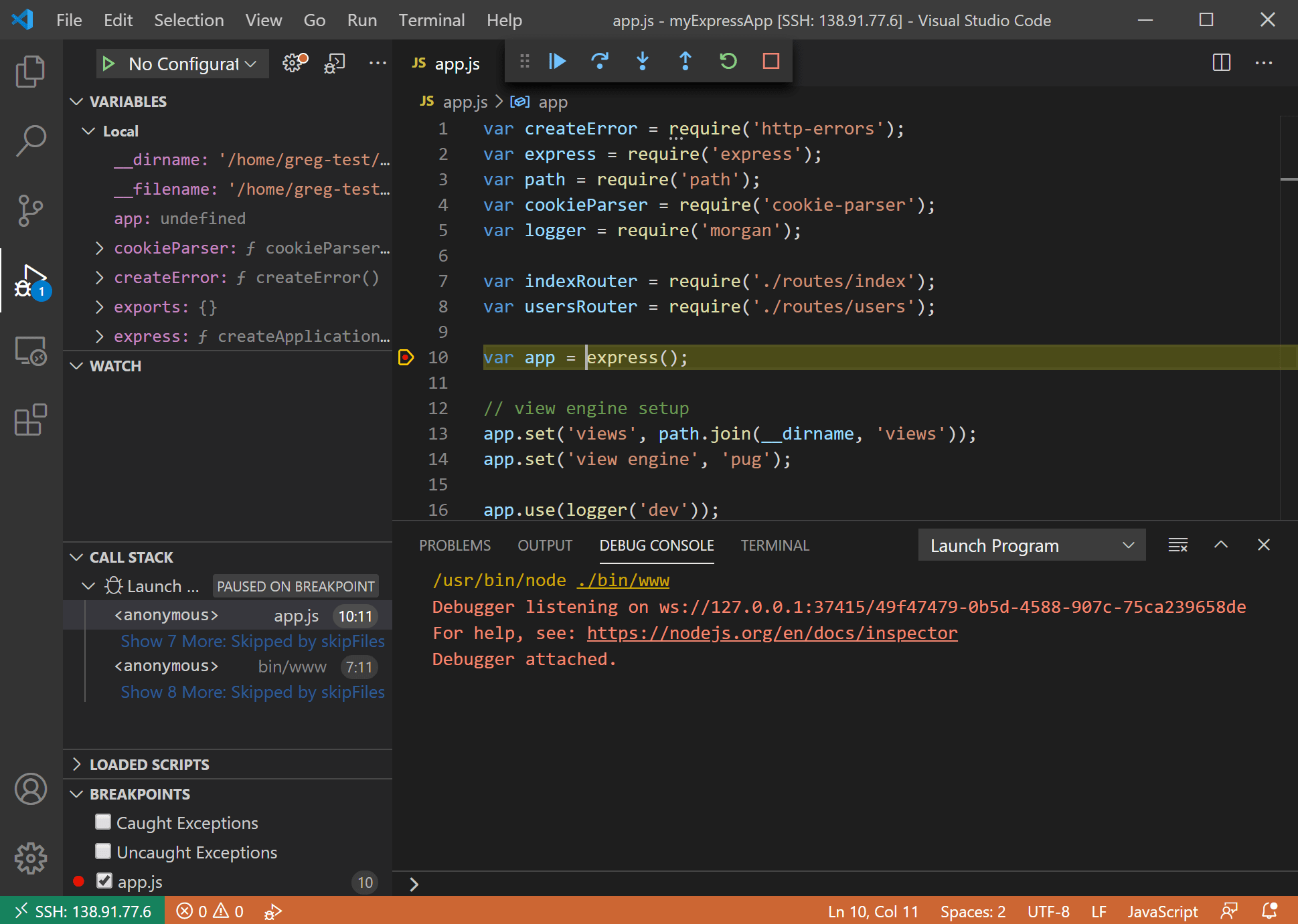
- OpenSSH: A widely used open-source SSH client and server.
- Putty: A popular SSH client for Windows users.
- Bitvise SSH Client: A commercial SSH client with advanced features.
- TunnelBear: A user-friendly SSH client for remote connections.
Step-by-Step Guide to Secure Connections
Establishing a secure connection between IoT devices using P2P SSH involves several steps. Below is a step-by-step guide to help you get started:
- Install an SSH client on your computer.
- Generate an SSH key pair for authentication.
- Configure the SSH server on your IoT device.
- Establish a secure connection between the devices.
- Test the connection to ensure it is working properly.
Tips for Successful Implementation
- Use strong passwords and encryption methods.
- Regularly update your SSH client and server software.
- Monitor your network for suspicious activity.
- Implement multi-factor authentication for added security.
Best Practices for Remote IoT Security
Ensuring the security of your remote IoT connections requires more than just using P2P SSH. It's important to follow best practices to minimize risks and protect your devices from cyber threats. Below are some best practices for remote IoT security:
Security Best Practices
- Use strong, unique passwords for all devices.
- Enable automatic software updates to ensure you have the latest security patches.
- Limit access to sensitive data and functions.
- Regularly audit your network for vulnerabilities.
Common SSH Pitfalls to Avoid
While P2P SSH is a powerful tool for secure remote connections, there are several pitfalls to avoid. By being aware of these common mistakes, you can ensure the security of your IoT devices and prevent potential issues.
Potential SSH Pitfalls
- Using weak passwords or default credentials.
- Failing to update software and firmware regularly.
- Not monitoring network activity for suspicious behavior.
- Ignoring security alerts and warnings.
Free SSH Tools for Remote IoT
If you're looking for free tools to securely connect remote IoT P2P SSH, there are several options available. These tools offer a range of features and capabilities, making it easy to find one that meets your needs. Below are some of the best free SSH tools for remote IoT connections:
Top Free SSH Tools
- OpenSSH: A robust, open-source SSH client and server.
- Putty: A lightweight SSH client for Windows users.
- WinSCP: A free SFTP and SCP client for Windows.
- FileZilla: A popular FTP and SFTP client for secure file transfers.
Case Studies of Successful Implementation
To better understand how securely connect remote IoT P2P SSH can be implemented in real-world scenarios, let's examine some case studies of successful implementations:
Case Study 1: Smart Home Security
A homeowner used P2P SSH to securely connect their smart home devices, ensuring that all communication between devices was encrypted and protected from unauthorized access. This setup allowed them to remotely monitor and control their devices while maintaining the highest level of security.
Case Study 2: Industrial IoT
An industrial company implemented P2P SSH to securely connect their IoT devices on the factory floor. This solution enabled them to monitor and manage their devices in real-time, improving efficiency and reducing downtime.
Conclusion and Next Steps
Securing your remote IoT connections is essential for protecting your devices and data from cyber threats. By using P2P SSH and following best practices for remote IoT security, you can establish a secure connection that ensures the integrity of your network. Remember to regularly update your software, monitor your network for suspicious activity, and implement multi-factor authentication for added security.
We encourage you to take the next step by downloading and installing a free SSH tool to start securing your remote IoT connections today. Don't forget to leave a comment or share this article with others who may benefit from the information. For more insights and tips on IoT security, explore our other articles on the topic.
Stay secure, stay informed, and keep your IoT devices protected!