In today's interconnected world, securely connecting remote IoT devices using peer-to-peer (P2P) SSH protocols is crucial to protect against potential hacker attacks. The rise of IoT devices has created new opportunities but also significant security risks. With billions of connected devices, ensuring secure communication between these devices is paramount to safeguard sensitive data and maintain privacy.
As IoT networks expand, the challenge of securing communications grows exponentially. Traditional methods often fall short, making it essential to adopt advanced solutions like P2P SSH. This approach offers robust encryption and secure connections that can thwart unauthorized access and malicious activities.
This article will delve into the intricacies of securely connecting IoT devices using P2P SSH, offering practical insights, expert tips, and actionable strategies. Whether you're a developer, IT professional, or simply someone interested in IoT security, this guide will equip you with the knowledge needed to protect your network from potential threats.
Read also:Jessica Lackmeyer A Rising Star In The World Of Entertainment And Modeling
Table of Contents
- Introduction to IoT Security
- Understanding P2P SSH in IoT
- Risks of Insecure IoT Connections
- Benefits of Secure Connections
- Setting Up Secure Connections
- Best Practices for IoT Security
- Tools and Technologies for Secure IoT
- Common Hacker Techniques
- Case Studies in IoT Security
- The Future of IoT Security
Introduction to IoT Security
The Internet of Things (IoT) has revolutionized how we interact with technology, creating a network of interconnected devices that enhance productivity and convenience. However, with this innovation comes the challenge of securing these devices against malicious actors. Securely connecting remote IoT devices using P2P SSH is one of the most effective strategies to mitigate risks.
IoT security involves protecting devices, networks, and data from unauthorized access and cyberattacks. As more devices connect to the internet, the attack surface expands, making it vital to implement robust security measures. This section will explore the foundational concepts of IoT security and why secure connections are essential.
Key Takeaways:
- IoT devices are vulnerable to cyberattacks due to their widespread connectivity.
- Securing IoT connections is crucial to protect sensitive data and maintain privacy.
- P2P SSH offers a secure method for encrypting communication between devices.
Understanding P2P SSH in IoT
What is P2P SSH?
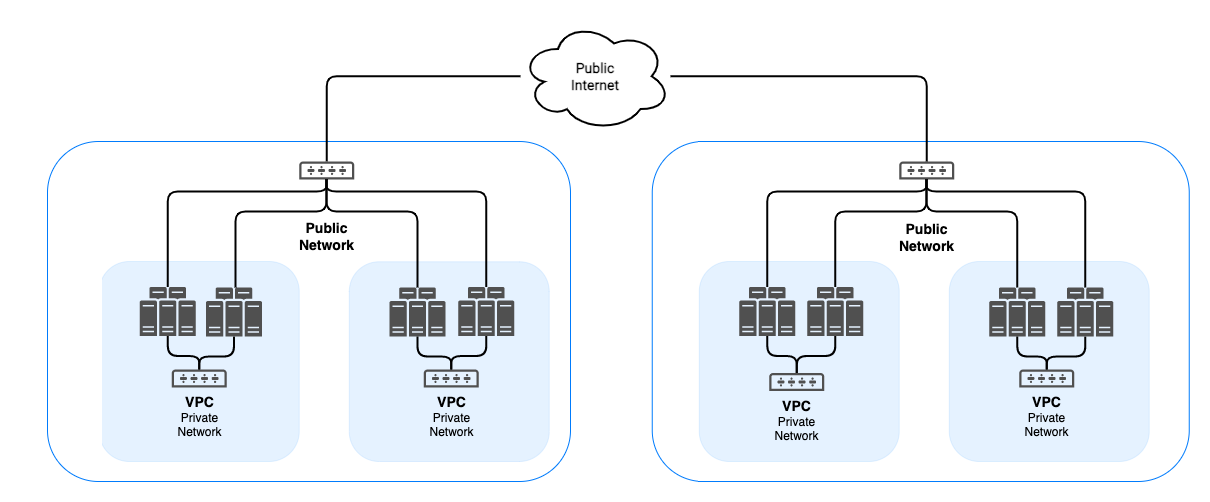
Peer-to-Peer (P2P) SSH is a secure communication protocol that allows devices to establish encrypted connections without relying on centralized servers. This method ensures that data transmitted between IoT devices remains private and protected from unauthorized access. By eliminating the need for intermediaries, P2P SSH reduces the risk of man-in-the-middle attacks and data breaches.
Benefits of P2P SSH:
- Enhanced security through end-to-end encryption.
- Reduced reliance on centralized infrastructure, minimizing single points of failure.
- Improved efficiency by enabling direct communication between devices.
How Does P2P SSH Work?
P2P SSH operates by creating secure tunnels between devices using cryptographic keys. These keys ensure that only authorized devices can access the network, preventing unauthorized access. The process involves key exchange, authentication, and encryption, all of which work together to secure the communication channel.
Read also:Josh Elliott What Is He Doing Now Unveiling His Current Ventures And Achievements
Data from SSH Communications Security highlights the importance of SSH in securing remote connections, making it a trusted choice for IoT networks.
Risks of Insecure IoT Connections
Insecure IoT connections pose significant risks to both individuals and organizations. Without proper security measures, devices can become entry points for hackers to infiltrate networks and access sensitive information. The consequences of such breaches can be severe, ranging from financial losses to reputational damage.
Common Risks:
- Data breaches leading to exposure of personal and confidential information.
- Malware infections that compromise device functionality and network security.
- Distributed Denial of Service (DDoS) attacks using compromised IoT devices.
A study by Gartner predicts that by 2025, over 75% of organizations will experience an IoT-based security breach, underscoring the urgency of implementing secure connections.
Benefits of Secure Connections
Implementing secure connections for IoT devices offers numerous advantages, including enhanced data protection, improved network reliability, and increased user trust. By adopting P2P SSH and other advanced security protocols, organizations can safeguard their networks against potential threats.
Key Benefits:
- Strong encryption to protect data during transmission.
- Authentication mechanisms to verify device identities.
- Reduced risk of cyberattacks, ensuring network integrity.
According to IBM Security, organizations that prioritize encryption and secure connections experience fewer security incidents and recover faster from breaches.
Setting Up Secure Connections
Step-by-Step Guide to Implementing P2P SSH
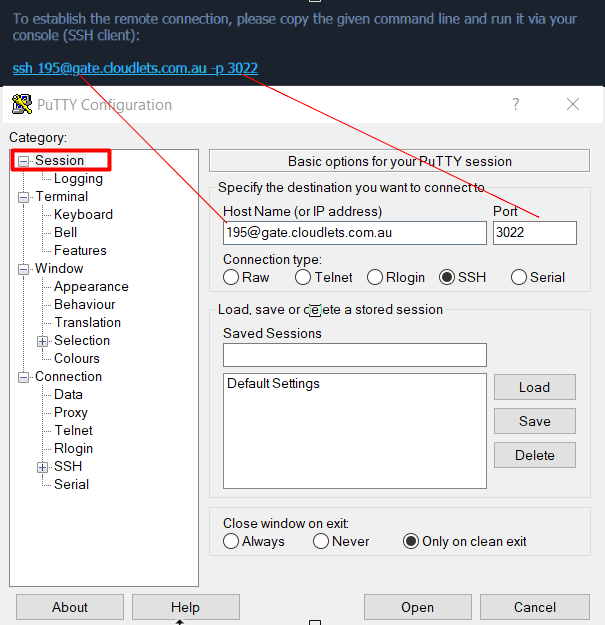
Setting up secure connections using P2P SSH involves several steps, each crucial to ensuring the integrity and security of your IoT network. Below is a comprehensive guide to help you implement this protocol effectively:
- Identify devices that require secure connections.
- Generate cryptographic keys for each device.
- Configure SSH settings to enable P2P communication.
- Test the connection to ensure secure data transmission.
Referencing best practices from Cisco IoT Security, this process ensures that your network remains protected against unauthorized access.
Best Practices for IoT Security
To maximize the security of your IoT network, it's essential to follow established best practices. These practices include regular updates, strong authentication, and continuous monitoring to detect and respond to potential threats.
Best Practices:
- Regularly update firmware and software to patch vulnerabilities.
- Implement multi-factor authentication for added security.
- Monitor network activity to identify and address suspicious behavior.
Data from NIST emphasizes the importance of continuous monitoring and proactive security measures in mitigating IoT risks.
Tools and Technologies for Secure IoT
Top Tools for IoT Security
Several tools and technologies can enhance the security of your IoT network. These include intrusion detection systems, firewalls, and encryption software designed specifically for IoT environments.
Recommended Tools:
- Wireshark – Network protocol analyzer for monitoring and analyzing traffic.
- OpenVAS – Vulnerability scanner for identifying weaknesses in your network.
- Nessus – Comprehensive vulnerability assessment solution.
Emerging Technologies
Blockchain and artificial intelligence are emerging as transformative technologies in IoT security. These innovations offer new ways to secure data and detect threats, further enhancing network protection.
Common Hacker Techniques
Hackers employ various techniques to exploit vulnerabilities in IoT networks. Understanding these methods is crucial to developing effective countermeasures. Below are some common hacker techniques:
- Brute force attacks targeting weak passwords.
- Phishing scams designed to steal login credentials.
- Exploiting unpatched vulnerabilities in device firmware.
Insights from Symantec Security Center reveal that phishing attacks account for over 80% of successful breaches, highlighting the importance of user awareness and training.
Case Studies in IoT Security
Case Study 1: Mirai Botnet Attack
The Mirai botnet attack in 2016 demonstrated the vulnerabilities of insecure IoT devices. By exploiting weak security measures, attackers were able to compromise thousands of devices, resulting in widespread internet outages.
Case Study 2: Smart Home Breach
A 2019 incident involving a smart home system highlighted the risks of inadequate authentication. Hackers gained access to the system, enabling them to control connected devices and compromise user privacy.
These case studies underscore the importance of implementing robust security measures, such as P2P SSH, to protect IoT networks.
The Future of IoT Security
As IoT technology continues to evolve, so too must security measures. The future of IoT security lies in adopting advanced solutions that address emerging threats and vulnerabilities. This includes integrating AI-driven analytics, blockchain-based authentication, and quantum-resistant encryption.
Research from IDC predicts that by 2030, over 50 billion IoT devices will be connected globally, necessitating scalable and secure solutions to manage this growth.
Conclusion
Securing IoT devices using P2P SSH is essential to protect against hacker attacks and ensure the integrity of your network. By understanding the risks, implementing best practices, and leveraging advanced tools and technologies, you can safeguard your IoT ecosystem effectively.
We encourage readers to take action by reviewing their current security measures and adopting P2P SSH where applicable. Feel free to leave a comment below or share this article with others who may benefit from its insights. For more information on IoT security, explore our other articles and resources.