In today's interconnected world, securely connect remote IoT VPC on AWS with Raspberry Pi is a critical skill for developers and IT professionals. The Internet of Things (IoT) continues to expand, and ensuring secure communication between devices is paramount. Whether you're managing smart home systems, industrial automation, or agricultural monitoring, secure connections are non-negotiable.
As the demand for remote access to IoT devices grows, so does the need for robust security measures. AWS provides a scalable and secure infrastructure for IoT deployments, while Raspberry Pi serves as an affordable and versatile platform for device management. Together, they form a powerful combination for building secure and efficient IoT systems.
This article will guide you through the process of setting up a secure connection between a remote IoT Virtual Private Cloud (VPC) on AWS and a Raspberry Pi. We'll cover essential topics such as network architecture, security best practices, and step-by-step configurations. By the end of this guide, you'll have the knowledge and tools to implement a secure IoT environment tailored to your needs.
Read also:Jellybean Leak A Comprehensive Guide To Understanding And Addressing The Issue
Table of Contents
- Introduction to IoT and Its Security Challenges
- AWS IoT Architecture and VPC Overview
- Setting Up Raspberry Pi for IoT
- Secure Connection Methods for IoT Devices
- Network Security Considerations
- Step-by-Step Configuration Guide
- Best Practices for Secure IoT Deployments
- Troubleshooting Common Issues
- Real-World Case Studies
- Conclusion and Next Steps
Introduction to IoT and Its Security Challenges
The Internet of Things (IoT) has revolutionized the way we interact with technology. From smart homes to industrial automation, IoT devices are transforming industries. However, with this innovation comes significant security challenges. As devices become more interconnected, they also become more vulnerable to cyber threats.
One of the primary concerns in IoT deployments is ensuring secure communication between devices and cloud platforms. Hackers can exploit vulnerabilities in IoT networks to gain unauthorized access, steal sensitive data, or disrupt critical operations. To mitigate these risks, organizations must implement robust security measures.
Why Security Matters in IoT
IoT security is not just a technical issue; it's a business imperative. Breaches in IoT networks can lead to financial losses, reputational damage, and legal liabilities. For example, a compromised smart home system could expose personal data, while a breach in industrial IoT could disrupt production lines.
AWS IoT Architecture and VPC Overview
AWS offers a comprehensive platform for IoT deployments, including the AWS IoT Core service and Virtual Private Cloud (VPC) for secure network isolation. AWS IoT Core enables secure and reliable communication between devices and the cloud, while VPC provides a private network environment for your IoT infrastructure.
Key Components of AWS IoT Architecture
- AWS IoT Core: A managed cloud platform that allows connected devices to interact with cloud applications and other devices securely.
- VPC: A virtual network dedicated to your AWS resources, allowing you to control access to your IoT devices.
- Identity and Access Management (IAM): A service that helps manage access to AWS services and resources securely.
Setting Up Raspberry Pi for IoT
Raspberry Pi is a popular choice for IoT projects due to its affordability, versatility, and ease of use. To securely connect your Raspberry Pi to an AWS IoT VPC, you'll need to configure it properly and ensure it meets security standards.
Steps to Set Up Raspberry Pi
- Install the latest version of Raspberry Pi OS on your device.
- Configure Wi-Fi or Ethernet settings for network connectivity.
- Enable SSH for remote access (optional but recommended for secure management).
- Update the system with the latest security patches and software updates.
Secure Connection Methods for IoT Devices
Securing IoT devices involves implementing multiple layers of protection. One of the most effective methods is using encrypted communication protocols such as Transport Layer Security (TLS) and Secure Sockets Layer (SSL). These protocols ensure that data transmitted between devices and the cloud remains confidential and tamper-proof.
Read also:5starsstockscom Ai Revolutionizing Investment Strategies For The Future
Encryption Protocols for IoT
- TLS: A widely used protocol for securing data in transit.
- SSL: An older but still relevant protocol for encrypting communications.
- MQTT over TLS: A lightweight messaging protocol commonly used in IoT applications.
Network Security Considerations
Network security is a critical aspect of IoT deployments. By isolating IoT devices in a dedicated VPC on AWS, you can control access and reduce the attack surface. Additionally, implementing firewalls, intrusion detection systems, and regular security audits can further enhance your network's resilience.
Best Network Security Practices
- Use strong authentication mechanisms, such as multi-factor authentication (MFA).
- Regularly update firmware and software to patch known vulnerabilities.
- Segment your network to isolate IoT devices from other critical systems.
Step-by-Step Configuration Guide
Configuring a secure connection between a Raspberry Pi and an AWS IoT VPC requires careful planning and execution. Below is a step-by-step guide to help you through the process:
Step 1: Set Up AWS IoT Core
Create an AWS account if you haven't already, and navigate to the AWS IoT Core console. Follow the instructions to set up a new IoT thing and generate necessary certificates and keys.
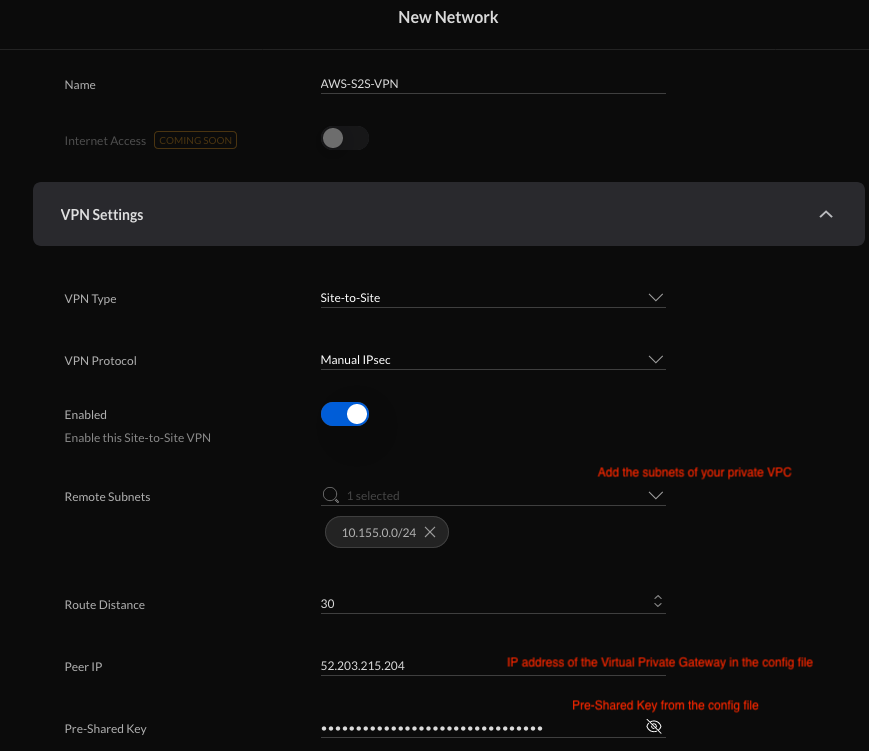
Step 2: Configure VPC
Create a new VPC in the AWS Management Console and configure subnets, route tables, and security groups to allow secure access to your IoT devices.
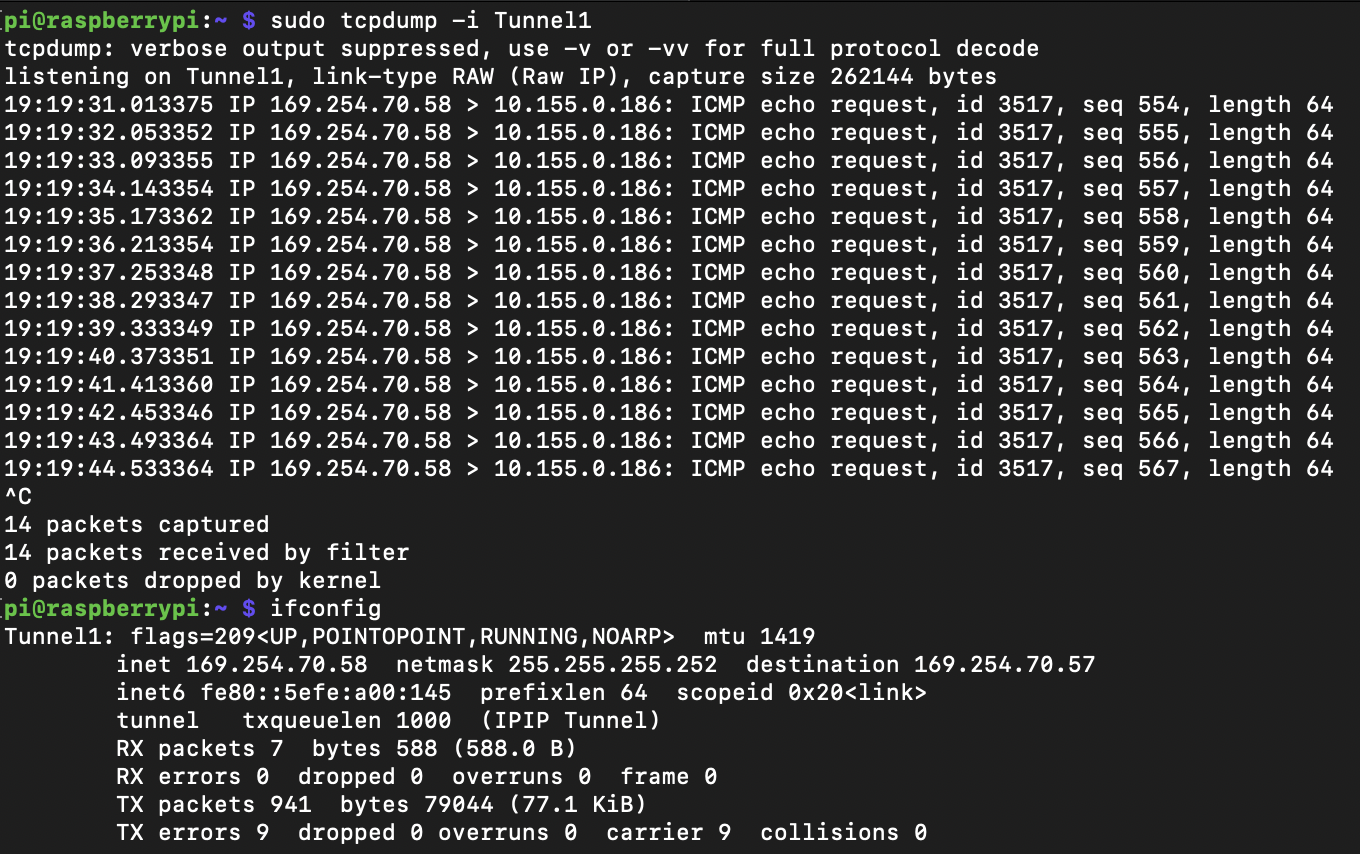
Step 3: Connect Raspberry Pi to AWS IoT
Install the AWS IoT SDK on your Raspberry Pi and use the generated certificates to establish a secure connection. Test the connection by publishing and subscribing to MQTT topics.
Best Practices for Secure IoT Deployments
Implementing best practices is essential for maintaining the security and reliability of your IoT systems. Below are some key recommendations:
- Regularly monitor network activity for suspicious behavior.
- Limit access to IoT devices to authorized personnel only.
- Conduct regular security assessments and penetration tests.
Troubleshooting Common Issues
Even with the best planning, issues can arise during IoT deployments. Below are some common problems and their solutions:
Connection Issues
If your Raspberry Pi cannot connect to AWS IoT, check the following:
- Ensure the correct certificates and keys are installed.
- Verify network settings and firewall rules.
- Check the AWS IoT Core configuration for errors.
Real-World Case Studies
Learning from real-world examples can provide valuable insights into successful IoT deployments. Below are two case studies that demonstrate the importance of secure connections in IoT:
Case Study 1: Smart Agriculture
Agricultural company XYZ implemented an IoT system to monitor soil moisture levels and automate irrigation. By securely connecting their Raspberry Pi sensors to an AWS IoT VPC, they ensured data integrity and reduced operational costs.
Case Study 2: Industrial Automation
Manufacturing firm ABC deployed IoT devices to monitor production line performance. Using AWS IoT Core and VPC, they achieved secure and reliable communication between devices, improving efficiency and reducing downtime.
Conclusion and Next Steps
Securing IoT deployments is crucial for protecting sensitive data and ensuring system reliability. By following the steps outlined in this guide, you can establish a secure connection between a remote IoT VPC on AWS and a Raspberry Pi. Remember to implement best practices and regularly review your security measures to adapt to evolving threats.
We encourage you to leave a comment or question below and share this article with others who may find it helpful. For more in-depth information, explore our other resources on IoT and cloud security.