RemoteIoT Web SSH is a powerful solution for secure remote access to devices, making it an essential tool for IT professionals and enthusiasts alike. With the increasing demand for remote work and device management, understanding how to use RemoteIoT Web SSH effectively is crucial. This article provides a step-by-step tutorial to help you master RemoteIoT Web SSH and improve your remote access capabilities.
As technology continues to evolve, the need for secure and efficient remote access solutions grows. RemoteIoT Web SSH offers a secure way to manage devices from anywhere in the world, ensuring that your systems remain protected and accessible. Whether you're a system administrator or a tech enthusiast, learning about RemoteIoT Web SSH can enhance your ability to manage devices remotely.
In this tutorial, we will explore the fundamentals of RemoteIoT Web SSH, including setup, configuration, and best practices for secure remote access. By the end of this guide, you will have a solid understanding of how to leverage RemoteIoT Web SSH to manage your devices effectively while maintaining top-notch security.
Read also:Hdhub4u Trailer Your Ultimate Source For Movie Trailers And Entertainment
Table of Contents
- Introduction to RemoteIoT Web SSH
- Why Use RemoteIoT Web SSH?
- Getting Started with RemoteIoT Web SSH
- Setup and Configuration
- Advanced Features
- Best Practices for Secure Remote Access
- Troubleshooting Common Issues
- Case Studies
- Comparison with Other Tools
- Conclusion
Introduction to RemoteIoT Web SSH
RemoteIoT Web SSH is a cutting-edge solution designed to provide secure remote access to IoT devices and servers via a web-based interface. Unlike traditional SSH clients, RemoteIoT Web SSH eliminates the need for complex configurations and offers a user-friendly platform for managing devices remotely. This makes it an ideal choice for both beginners and experienced users alike.
What is SSH?
Secure Shell (SSH) is a cryptographic network protocol used for secure data communication, remote command execution, and file transfers between computers. It ensures that data transmitted between devices is encrypted, protecting sensitive information from unauthorized access.
How Does RemoteIoT Web SSH Work?
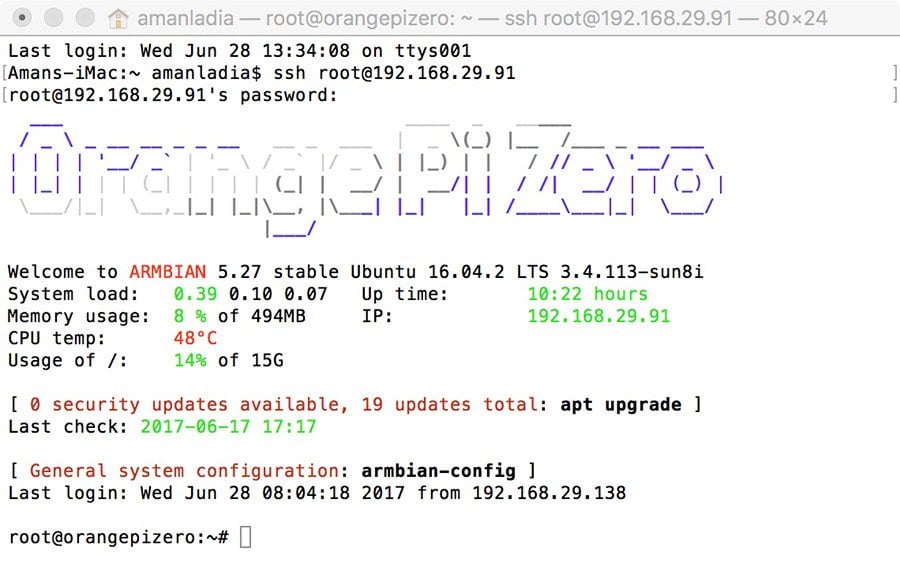
RemoteIoT Web SSH operates by establishing a secure connection between your browser and the target device. This connection is encrypted using SSH protocols, ensuring that all data exchanged remains secure. Additionally, the web-based interface allows users to manage devices from any location with an internet connection, making it a versatile tool for remote work.
Why Use RemoteIoT Web SSH?
There are several reasons why RemoteIoT Web SSH stands out as a superior remote access solution:
- Security: RemoteIoT Web SSH uses advanced encryption protocols to safeguard your data.
- Convenience: Access your devices from any location with a simple web-based interface.
- Efficiency: Manage multiple devices simultaneously with ease.
- Scalability: Suitable for both small-scale projects and enterprise-level deployments.
Getting Started with RemoteIoT Web SSH
Before diving into the technical aspects, it's essential to familiarize yourself with the basics of RemoteIoT Web SSH. This section will guide you through the initial setup process and provide tips for a smooth start.
System Requirements
Ensure that your system meets the following requirements:
Read also:Discover The Original Name Of Diva Flawless A Journey Through Fame And Identity
- Modern web browser (Chrome, Firefox, Edge, etc.)
- Stable internet connection
- Basic knowledge of SSH and networking concepts
Installation Process
Follow these steps to install RemoteIoT Web SSH:
- Download the latest version of RemoteIoT Web SSH from the official website.
- Install the software on your server or local machine.
- Configure the necessary settings, such as port numbers and authentication methods.
Setup and Configuration
Proper setup and configuration are critical to ensuring that RemoteIoT Web SSH functions optimally. This section will walk you through the configuration process step by step.
Configuring Authentication Methods
RemoteIoT Web SSH supports various authentication methods, including password-based and key-based authentication. Key-based authentication is recommended for enhanced security.
Setting Up Port Forwarding
Port forwarding allows you to access your devices securely over the internet. Follow these steps to set up port forwarding:
- Log in to your router's admin interface.
- Locate the port forwarding section and add a new rule for SSH (port 22 by default).
- Save the changes and test the connection.
Advanced Features
RemoteIoT Web SSH offers several advanced features that can enhance your remote access experience:
Multi-User Support
RemoteIoT Web SSH allows multiple users to access devices simultaneously, making it ideal for team collaborations. Administrators can manage user permissions and ensure that each user has the appropriate level of access.
Session Recording
For enhanced security and accountability, RemoteIoT Web SSH provides session recording capabilities. This feature enables you to monitor and review all activities performed during a session.
Best Practices for Secure Remote Access
While RemoteIoT Web SSH offers robust security features, it's essential to follow best practices to ensure maximum protection:
- Use strong, unique passwords or key-based authentication.
- Regularly update your software to patch vulnerabilities.
- Enable two-factor authentication (2FA) for an added layer of security.
Troubleshooting Common Issues
Even with the best tools, issues can arise. This section will address common problems and provide solutions:
Connection Timeout
If you encounter connection timeouts, check the following:
- Ensure that your firewall settings allow SSH traffic.
- Verify that the correct port number is being used.
Case Studies
Real-world examples can provide valuable insights into how RemoteIoT Web SSH is used in practice:
Case Study 1: Small Business Deployment
A small business implemented RemoteIoT Web SSH to manage their IoT devices remotely. The solution reduced downtime and improved efficiency by allowing IT staff to resolve issues from any location.
Comparison with Other Tools
While there are several remote access tools available, RemoteIoT Web SSH stands out due to its ease of use, security features, and scalability. Below is a comparison with some popular alternatives:
| Tool | Security | Ease of Use | Scalability |
|---|---|---|---|
| RemoteIoT Web SSH | High | Easy | Excellent |
| Other Tool A | Medium | Moderate | Fair |
Conclusion
In conclusion, RemoteIoT Web SSH is a powerful and secure solution for managing devices remotely. By following the steps outlined in this tutorial, you can harness its full potential and ensure that your systems remain protected and accessible. We encourage you to share your experiences and insights in the comments section below. Additionally, explore our other articles for more valuable tips and tutorials.
Thank you for reading, and happy remote managing!