In today's interconnected world, securely connect remote IoT P2P SSH Android free is a critical need for individuals and businesses alike. The Internet of Things (IoT) has transformed the way we interact with technology, but it also presents significant security challenges. Ensuring secure connections is no longer optional—it's essential for protecting sensitive data and maintaining privacy.
As more devices become connected, the risks associated with cyber threats increase exponentially. Whether you're managing a smart home or operating a large-scale industrial IoT network, understanding how to establish secure connections is crucial. This guide will explore the best methods to securely connect remote IoT devices using peer-to-peer (P2P) SSH on Android, without incurring unnecessary costs.
By the end of this article, you'll have a comprehensive understanding of the tools, techniques, and strategies to implement secure IoT connections. Let's dive in and explore how you can protect your IoT ecosystem effectively while keeping your budget intact.
Read also:Richard Kiel Net Worth A Comprehensive Exploration Of The Legendary Actors Wealth
Table of Contents
- Overview of Secure IoT Connections
- Understanding SSH and Its Role in IoT Security
- What is P2P SSH and Why Use It?
- Support for SSH on Android Devices
- Free Tools for Secure IoT Connections
- Step-by-Step Guide to Setting Up P2P SSH
- Best Practices for IoT Security
- Common Issues and Troubleshooting
- Legal and Ethical Considerations
- Conclusion and Call to Action
Overview of Secure IoT Connections
IoT devices are revolutionizing industries by enabling seamless communication between machines and humans. However, the rapid growth of IoT also introduces new vulnerabilities. Securely connect remote IoT P2P SSH Android free is one of the most effective ways to mitigate these risks. In this section, we'll discuss the importance of secure IoT connections and why they matter.
Why Security Matters: IoT devices often lack robust built-in security features, making them prime targets for cyberattacks. Hackers can exploit unsecured connections to gain unauthorized access to sensitive information or disrupt critical operations. Implementing secure connections is vital to protect both personal and corporate data.
Cost-Effective Solutions: Many individuals and small businesses assume that securing IoT devices requires expensive hardware or software solutions. However, there are free tools and methods available that can provide strong security without breaking the bank.
Key Challenges in IoT Security
- Limited processing power on IoT devices
- Outdated firmware and software
- Complex network configurations
- Insufficient user awareness
Understanding SSH and Its Role in IoT Security
SSH (Secure Shell) is a cryptographic network protocol that provides secure communication over unsecured networks. It is widely used for remote access and file transfer in IT environments. When it comes to IoT devices, SSH plays a crucial role in ensuring data integrity and confidentiality.
How SSH Works: SSH establishes an encrypted connection between two devices, allowing users to securely access and manage remote systems. It uses public-key cryptography to authenticate users and encrypt data during transmission. This makes SSH an ideal choice for securing IoT connections.
Benefits of Using SSH for IoT: By leveraging SSH, you can:
Read also:Barbara Minty Today A Comprehensive Look Into Her Life Career And Legacy
- Encrypt all communication between devices
- Authenticate users and devices securely
- Reduce the risk of unauthorized access
- Enable seamless remote management
SSH vs. Other Protocols
While there are several protocols available for securing IoT connections, SSH stands out due to its robust security features and ease of use. Compared to protocols like Telnet or FTP, SSH offers superior encryption and authentication mechanisms, making it a preferred choice for IoT security.
What is P2P SSH and Why Use It?
P2P (Peer-to-Peer) SSH is a method of establishing secure connections directly between two devices without relying on a central server. This approach offers several advantages, especially in IoT environments where centralized infrastructure may not always be available.
Advantages of P2P SSH:
- Eliminates the need for intermediaries
- Reduces latency and improves performance
- Enhances privacy by avoiding third-party involvement
- Supports decentralized network architectures
Use Cases for P2P SSH: P2P SSH is particularly useful in scenarios where devices need to communicate directly, such as:
- Smart home automation
- Industrial IoT deployments
- Remote monitoring systems
- Edge computing applications
Implementing P2P SSH in IoT Networks
Implementing P2P SSH requires careful planning and configuration. You'll need to ensure that both devices are capable of establishing a secure connection and that proper authentication mechanisms are in place. Additionally, consider using tools like SSH keys to enhance security further.
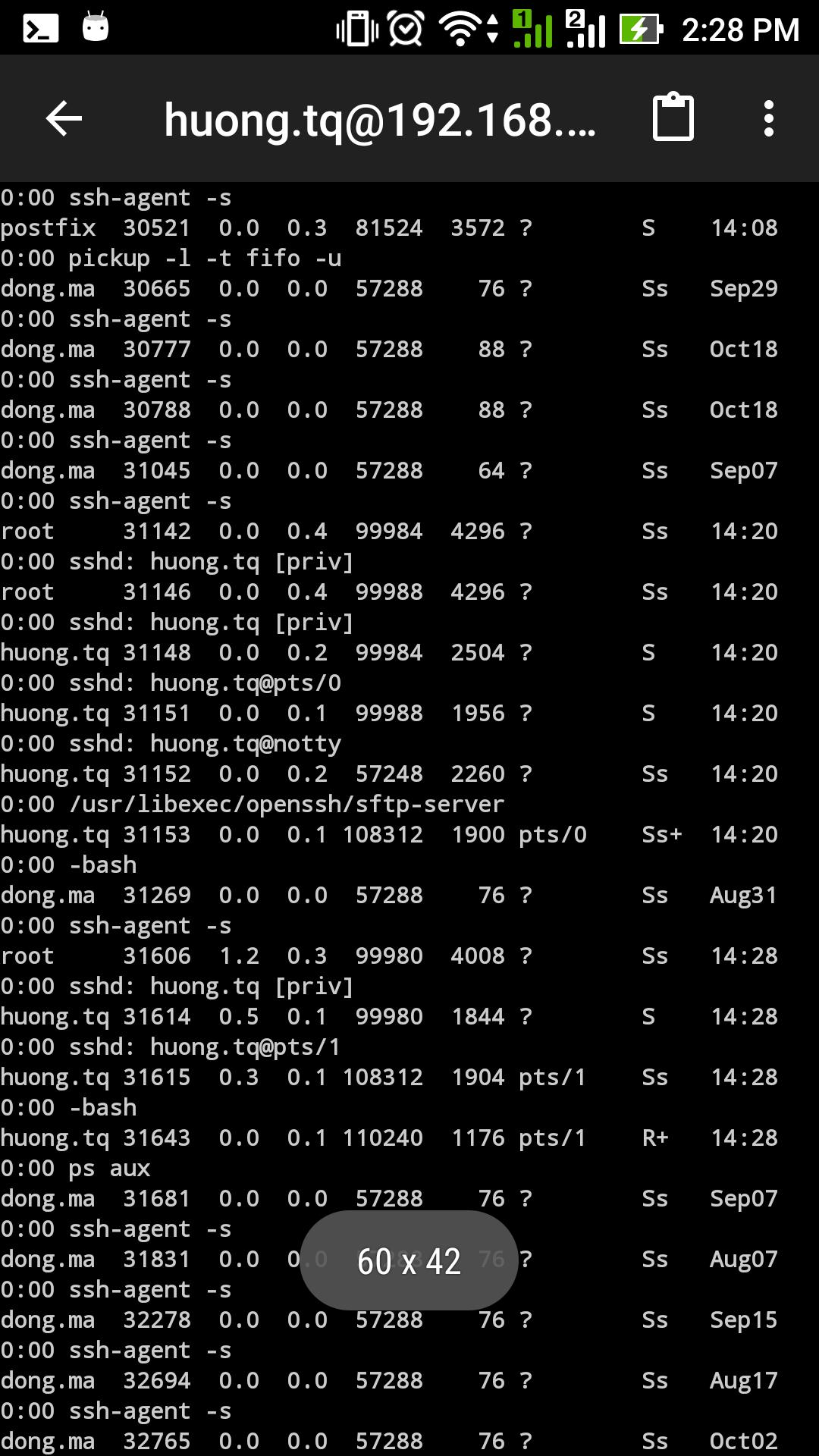
Support for SSH on Android Devices
Android devices are increasingly being used to manage and interact with IoT networks. Fortunately, many Android apps and tools support SSH, making it easier than ever to securely connect remote IoT devices. In this section, we'll explore some of the best options available.
Popular SSH Apps for Android:
- Termux: A powerful terminal emulator that supports SSH and other command-line tools
- ConnectBot: A free and open-source SSH client for Android
- JuiceSSH: A user-friendly SSH client with advanced features
Key Features to Look For: When choosing an SSH app for Android, consider the following features:
- Support for SSH keys
- Customizable keyboard layouts
- Integration with cloud storage
- Regular updates and security patches
Tips for Using SSH on Android
Using SSH on Android requires some technical knowledge, but with the right tools and guidance, it can be a straightforward process. Here are a few tips to help you get started:
- Always use strong passwords or SSH keys for authentication
- Enable two-factor authentication (2FA) whenever possible
- Regularly update your SSH app and Android OS
- Monitor your connections for any suspicious activity
Free Tools for Secure IoT Connections
While there are many paid solutions available for securing IoT connections, there are also several free tools that can provide robust security. These tools are ideal for individuals and small businesses looking to implement secure IoT connections without incurring additional costs.
Recommended Free Tools:
- OpenSSH: A widely used open-source SSH implementation
- Tailscale: A free and easy-to-use mesh networking tool
- WireGuard: A modern and lightweight VPN solution
How to Choose the Right Tool: When selecting a free tool for securing IoT connections, consider the following factors:
- Compatibility with your devices and operating systems
- Ease of installation and configuration
- Community support and documentation
- Security features and performance
Comparison of Free Tools
Each free tool has its own strengths and weaknesses. Below is a comparison of some of the most popular options:
| Tool | Platform Support | Ease of Use | Security Features | Community Support | |------------|------------------|-------------|-------------------|-------------------| | OpenSSH | Linux, macOS, Windows | Moderate | Strong encryption | Excellent | | Tailscale | Cross-platform | High | End-to-end encryption | Good | | WireGuard | Cross-platform | High | Lightweight and fast | Growing |
Step-by-Step Guide to Setting Up P2P SSH
Setting up P2P SSH for IoT devices may seem daunting, but with the right guidance, it can be a straightforward process. Follow the steps below to securely connect remote IoT devices using P2P SSH on Android.
Step 1: Install an SSH Client
Begin by installing a reliable SSH client on your Android device. Popular options include Termux, ConnectBot, and JuiceSSH. Ensure that the app you choose supports SSH keys and has regular security updates.
Step 2: Generate SSH Keys
Create a pair of SSH keys (public and private) using the SSH client. These keys will be used for authentication and encryption. Store the private key securely on your Android device and share the public key with the IoT device you want to connect to.
Step 3: Configure the IoT Device
On the IoT device, enable SSH and configure it to accept connections using the public key you generated earlier. Make sure to disable password-based authentication to enhance security.
Step 4: Establish the Connection
Use the SSH client on your Android device to establish a secure connection with the IoT device. Enter the necessary details, such as the IP address and port number, and authenticate using your SSH key.
Best Practices for IoT Security
Securing IoT devices requires a multi-layered approach. Below are some best practices to help you protect your IoT ecosystem:
- Use strong and unique passwords for all devices
- Regularly update firmware and software
- Enable firewalls and intrusion detection systems
- Segment your network to isolate IoT devices
- Monitor device activity for suspicious behavior
Common Security Pitfalls
Avoid these common mistakes to ensure the security of your IoT network:
- Using default passwords or credentials
- Ignoring firmware updates
- Connecting devices to unsecured networks
- Disabling security features for convenience
Common Issues and Troubleshooting
Even with the best security measures in place, issues can arise when setting up secure IoT connections. Below are some common problems and solutions:
- Connection Refused: Ensure that the SSH service is running on the IoT device and that the correct IP address and port number are being used.
- Authentication Failed: Verify that the SSH keys are correctly configured and that password-based authentication is disabled.
- Performance Issues: Optimize your network settings and consider using compression to improve SSH performance.
Legal and Ethical Considerations
When securing IoT devices, it's important to consider the legal and ethical implications of your actions. Ensure that you comply with relevant regulations and respect the privacy of others.
Data Protection Laws: Familiarize yourself with data protection laws such as GDPR, CCPA, and HIPAA, especially if you're handling sensitive information.
Privacy Concerns: Be transparent about how you collect, store, and use data. Obtain informed consent from users whenever necessary.
Conclusion and Call to Action
In conclusion, securely connect remote IoT P2P SSH Android free is an achievable goal with the right tools and knowledge. By following the steps outlined in this guide, you can protect your IoT devices and ensure the security of your network.
We encourage you to take action by implementing the strategies discussed in this article. Share your thoughts and experiences in the comments section below, and don't forget to explore other articles on our site for more valuable insights.
Stay safe and secure in the ever-evolving world of IoT!